Attacks
LFR via SSRF in BookStack: Beware of insecure-by-default libraries!


Security researcher
6 min
Switching from blind SSRF to local file read. Have you ever thought about it? Browsing the Internet, I found a third-party library called Intervention Image. It is a PHP image management and manipulation library that provides a simple interface for loading, storing and editing images.
The disturbing thing is that, while reading about this library, I noticed that it was referred to as "vulnerable by default." To understand it better, I wanted to exploit it, and what better way than in the real world?
Vulnerability
I searched on GitHub which sites used Intervention Image. I then found a repository that had a lot of interaction and good stars, so I decided to work with that one. The repository in question is BookStack. The vulnerability I’ll demonstrate is in version 23.10.2.
I will now show you the exploitation path from the source to the sink. This way you will understand the unexpected payload we will use to exploit this vulnerability.
From source to sink
On an account with writer permissions, you can create books and, within them, fill your pages. Such pages accept Markdown and HTML code. I show that process in this video:
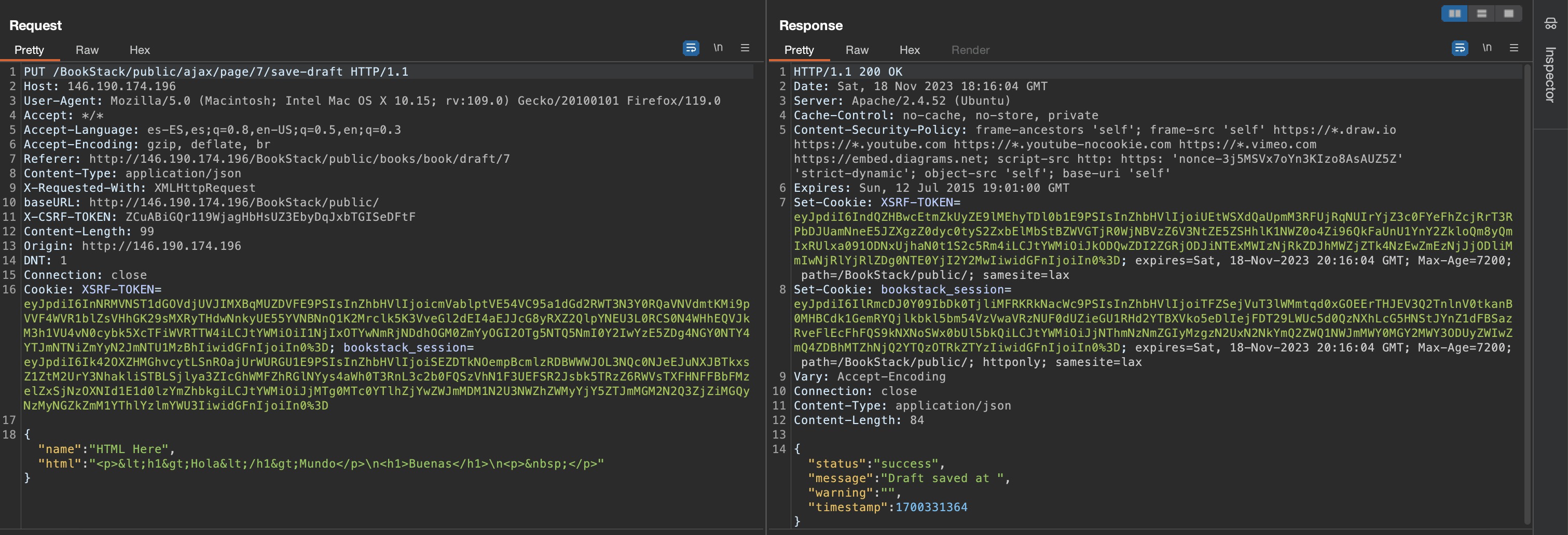
This is how that request looks like:
When we upload HTML (in this case) through a page, that HTML is handled here:
In the previous fragment, we see the methods involved in handling the HTML that we send to the application through a page of a book. Of all these methods, there is one that is of special interest, which is saveNewFromData. Let's look at it:
From this code fragment, we are only interested in loadGalleryThumbnailsForImage. Let's examine it now:
Finally, we have arrived at the sink, this is where we pass the base64 encoded data that we have sent in the src of the img tags in the HTML of the book page. We know that we have absolute control of the string that is passed to this method but... what can we do with that?
Exploit path
Remember I told you that intervention->make is vulnerable by default? Well, I want you to see why with your own eyes:
The make method can receive various types of data. Fortunately, it accepts URLs, which indicates that our input is valid.
Now that you have the exploit path, you can clearly see how we have gone from $this->intervention->make($imageData); to @file_get_contents($url, false, $context). We have complete control of the URL. This means we can perform SSRF attacks to interact with internal resources, etc.
However, it would be great if we could escalate this. Fortunately, there is a technique to filter the contents of arbitrary files using the php:// wrapper even if the output of the file read is not given to the user. This technique is called Blind File Oracles and was first discovered in DownUnderCTF 2022.
Summarizing, with a simple modification of the script php_filter_chains_oracle_exploit we can use the technique to filter the content of any file on the server.
Exploitation
The above script works with urlencode-based requests. Our case is different, because the requests are sent in JSON format. So, I simply changed the encoding of the request to urlencode, and it worked. That is perfect because it simplifies a lot the work and time spent to modify the script.
It is important to note that the exploit can be sent to either of these two endpoints in the parameter html:
In my case I preferred to do it with the first endpoint. The first endpoint is a temporary save, and the second endpoint is when we save the page as such. I recommend before using the script, that you verify from Burp Suite if the input actually reaches the sink, because it may not happen due to internal cache rules.
Finally, we only have to assign the necessary cookies to the script, the path, the HTTP verb, the file we want to read, and wait for the result. Watch me execute the script here:
In the following screenshot, you can see that I got the file /etc/passwd partially leaked:

We assigned this vulnerability the CVE ID CVE-2023-6199 and a CVSS score of 7.1. Read our advisory here.
No fix available yet but here's a workaround
There is currently no patch for Intervention Image addressing its vulnerability. However, if you are using this library, the best way to ensure you are not vulnerable is by never passing user data directly into the constructor. If you want to turn an upload into an image, pass the file path to the uploaded tempfile instead.
Conclusion
As always, extreme curiosity leads me to delve into applications to such an extent that I discover new ways to exploit vulnerabilities or to find rather peculiar sinkholes. In this blog post, we have seen how being able to edit HTML or Markdown content can lead to more critical vulnerabilities such as an arbitrary file read (in this case), instead of the typical cross-site scripting (XSS).
Remember that at Fluid Attacks we offer a solution to search for security vulnerabilities in software continuously. Secure your applications in a 21-day free trial of our automated security testing. You can upgrade at any time to include assessments by our pentesters.
Get started with Fluid Attacks' PTaaS right now
Other posts


























