Calibre Web 0.6.24 - ReDoS
8.7
High
Discovered by

Offensive Team, Fluid Attacks
Summary
Full name
Calibre Web 0.6.24 & Autocaliweb 0.7.0 - ReDoS
Code name
State
Public
Release date
Affected product
Calibre Web
Affected version(s)
Version 0.6.24 (Nicolette)
Vulnerability name
Asymmetric denial of service - ReDoS
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:N/VI:N/VA:H/SC:N/SI:N/SA:N
CVSS v4.0 base score
8.7
Exploit available
Yes
CVE ID(s)
Description
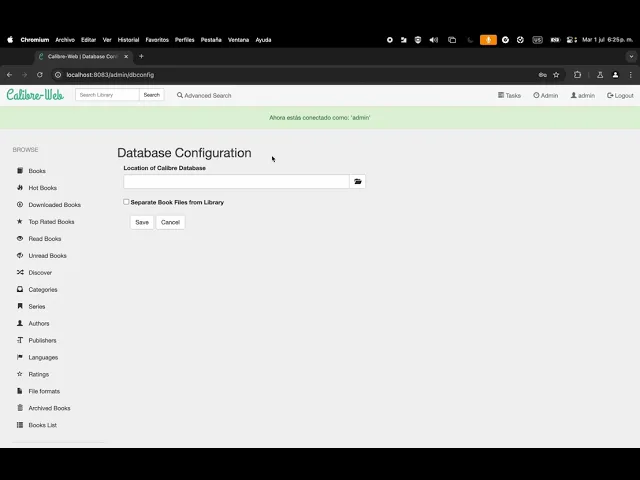
A ReDoS vulnerability has been identified in version 0.6.24 (Nicolette) of the Calibre Web web application, located in the cps/string_helper.py file. This allows unauthenticated users to cause disruption simply by crafting and sending a payload while attempting to log in. The Autocaliweb version 0.7.0 has also been confirmed as vulnerable to the same attack.
Vulnerability
The issue lies in the strip_whitespaces() function in the cps/string_helper.py file, which uses a regular expression that is vulnerable to catastrophic backtracking when processing specially crafted input. This function is applied directly to the username parameter, both during login and as part of the rate-limiting logic via @limiter.limit(), making it exploitable without authentication.
This causes the backend to hang for a significant amount of time.
PoC
Evidence of Exploitation
Notice that using the same quantity of characters as a payload doesn't bring down the server, unlike using the ReDoS payload.
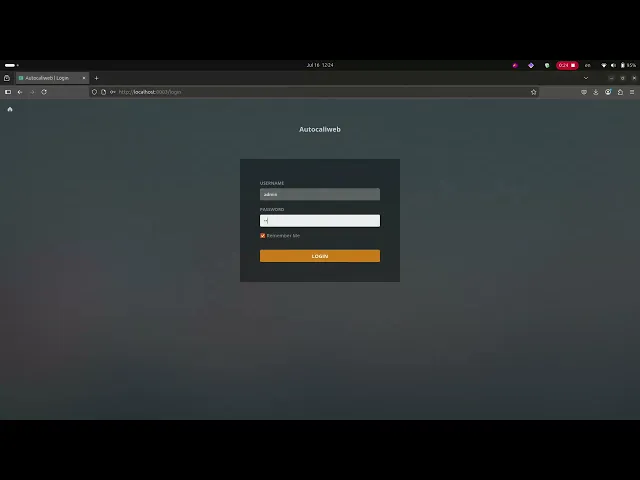
Autocaliweb is also vulnerable to the same attack:
Our security policy
We have reserved the ID CVE-2025-6998 to refer to this issue from now on.
System Information
Calibre Web:
Version 0.6.24 (Nicolette)
Operating System: Any
Autocaliweb:
Version 0.7.0
References
Calibre Web:
Github Repository: https://github.com/janeczku/calibre-web
Autocaliweb:
Github Repository: https://github.com/gelbphoenix/autocaliweb
Security: https://github.com/gelbphoenix/autocaliweb/security/policy
Mitigation
There is currently no patch available for this vulnerability on Calibre Web project.
Autocaliweb version 0.7.1 has patched this vulnerability.
Credits
The vulnerability was discovered by Johan Giraldo from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.