Calix GigaCenter ONT (Broadcom SoC) - Excessive Privileges
7
High
Discovered by
External Pentester
Summary
Full name
Excessive Privileges in Gigacenters ONT allows unauthenticated root access via UART
Code name
State
Public
Release date
Affected product
Calix GigaCenter ONT (Broadcom SoC)
Vendor
Calix
Affected version(s)
844E, 844G, 844GE, 854GE, 812G, 813G, and 818G
Fixed version(s)
R12.2.13.4 patch available to authorised users
Vulnerability name
Excessive Privileges
Vulnerability type
Remotely exploitable
No
CVSS v4.0 vector string
CVSS:4.0/AV:P/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N
CVSS v4.0 base score
7.0
Exploit available
No
CVE ID(s)
Description
The Calix GigaCenter ONT 844E, 844G, 844GE, 854GE, 812G, 813G, and 818G are affected by a vulnerability in the router’s firmware design, which allows unauthenticated root access via the UART debugging interface connected to the Broadcom SoC. The UART console does not require any credentials, enabling an attacker with physical access to the device to gain full control of the system.
Vulnerability
Steps to reproduce the vulnerability:
Disassemble the router.
Identify UART interfaces.
There are two sets of UART pins on the PCB:
One is located near the edge of the PCB (UART for the Broadcom SoC).
The other is located near the SoC and Serial Flash memory (UART for the Quantenna SoC).
In the image below you see the UART for the Quantenna SoC:

Gain root access without authentication.
Connect to the UART interface located near the SoC and Serial Flash.
Set the baud rate to 115200.
This grants access to a full root shell via UART.
A USB to UART interface, such as a Bus Pirate or FTDI, can be used to establish the connection.
Access confidential information and modify the system.
View sensitive data such as: User accounts, /etc/passwd content, Configuration files, firmware, webapp code
Since you have root access, you can: Create backdoors, enable/modify system services, and make persistent changes to the firmware.
Exploit
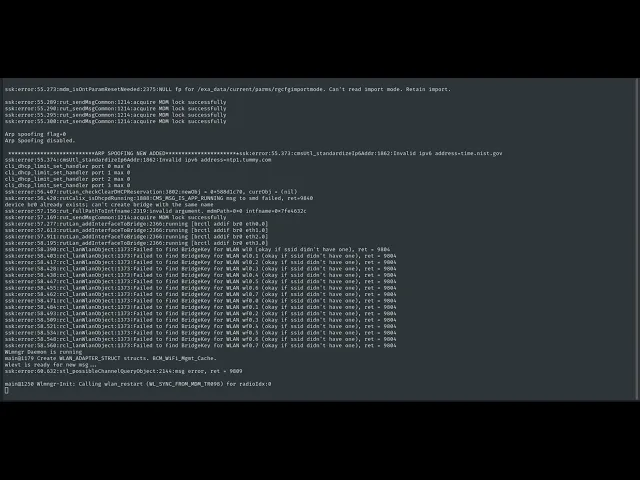
Connect a UART-USB interface to the Broadcom SoC UART interface and receive a root shell directly:

Evidence of Exploitation
Our security policy
We have reserved the ID CVE-2025-53914 to refer to this issue from now on.
System Information
Calix GigaCenter ONT 844E, 844G, 844GE, 854GE, 812G, 813G, and 818G.
References
Vendor: https://www.calix.com
Security: https://www.calix.com/security.html
Researcher's blog: https://revers3everything.com/calix-case-five-0-days-five-cves/
Mitigation
This issue is resolved in the R12.2.13.4 patch available to authorised users. Subscribers with concerns about the security of the ONT servicing their premises should contact their BSP to push the update, as these devices are not licensed to consumers.
Credits
The vulnerability was discovered by Danilo Erazo, an independent security researcher.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Vendor confirmed
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.








