
NestJS 11.1.13 - Lack of data validation allowing authentication/authorization bypass
8.2
High
Discovered by

Offensive Team, Fluid Attacks
Summary
Full name
NestJS 11.1.13 - Lack of data validation allowing authentication/authorization bypass
Code name
State
Public
Release date
Affected product
nest.js
Vendor
nest.js
Affected version(s)
11.1.13
Fixed version(s)
11.1.14
Package manager
npm
Vulnerability name
Lack of data validation
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:P/PR:N/UI:N/VC:N/VI:H/VA:N/SC:N/SI:N/SA:N
CVSS v4.0 base score
8.2
Exploit available
Yes
CVE ID(s)
Description
A NestJS application using @nestjs/platform-fastify can allow bypass of authentication/authorization middleware when Fastify path-normalization options (e.g., ignoreTrailingSlash, ignoreDuplicateSlashes, useSemicolonDelimiter) are enabled. In affected route-scoped middleware setups, variant paths may skip middleware checks while still reaching the protected handler.
Vulnerability
The bug is a path canonicalization mismatch between middleware matching and route matching in Nest’s Fastify adapter.
Nest passes Fastify routerOptions (such as ignoreTrailingSlash, ignoreDuplicateSlashes, and useSemicolonDelimiter) to the Fastify router in packages/platform-fastify/adapters/fastify-adapter.ts:253.
But middleware execution is decided by a separate regex check over req.originalUrl in packages/platform-fastify/adapters/fastify-adapter.ts:706 and packages/platform-fastify/adapters/fastify-adapter.ts:713.
If that regex does not match, Nest does next() and skips the middleware (packages/platform-fastify/adapters/fastify-adapter.ts:714), while Fastify may still normalize the same path and route it to the protected handler. So the vulnerability exists because security checks (middleware) and request dispatch(router) use different URL interpretations.
This is a fail-open design issue (inconsistent normalization), not just a bad app config: non-default router options make the mismatch reachable.
PoC
Use the following code for the PoC
Send baseline request (should be blocked)
Send variant paths (bypass)
Control request with an auth header
Evidence of Exploitation
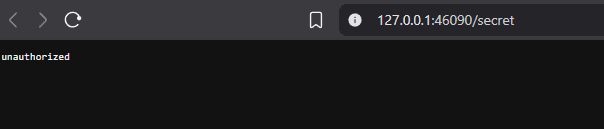
Unauthorized
Bypass
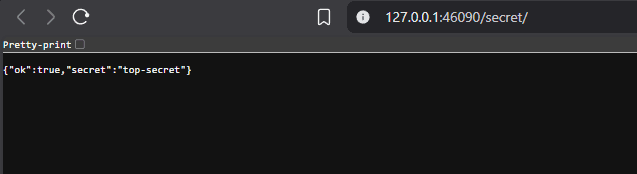
PoC
Our security policy
We have reserved the ID CVE-2026-2293 to refer to this issue from now on.
System Information
NestJS
Version 11.1.13
Operating System: Any
References
Product: https://github.com/nestjs/nest
Security: https://github.com/nestjs/nest/security
Mitigation
An updated version of Nest.js is available at the vendor page.
Credits
The vulnerability was discovered by Cristian Vargas from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Vendor confirmed
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.














