Frappe Framework v16.10.0 - Stored DOM XSS in Multiple Field Formatters
4.6
Medium
Detected by

Fluid Attacks AI SAST Scanner
Disclosed by
Oscar Uribe
Summary
Full name
Frappe Framework v16.10.0 - Stored DOM XSS in Multiple Field Formatters
Code name
State
Public
Release date
Affected product
Frappe
Vendor
Frappe
Affected version(s)
16.10.0
Fixed version(s)
16.16.0
Vulnerability name
Stored cross-site scripting (XSS)
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:A/VC:N/VI:N/VA:N/SC:L/SI:L/SA:N
CVSS v4.0 base score
4.6
Exploit available
Yes
CVE ID(s)
Description
An authenticated attacker can persist crafted values in multiple field types and trigger client-side script execution when another user opens the affected document in Desk. The vulnerable formatter implementations interpolate stored values into raw HTML attributes and element content without escaping
Validated affected formatters:
Color.
Icon.
Vulnerability
The vulnerable path is:
Source: attacker-controlled field values for formatter-backed fields are submitted through the normal web flow and tampered with in transit
Persistence: the backend stores the crafted values because these field types are not strictly server-validated against their expected allowlists, and the HTML sanitizer is not triggered for payloads without < or >.
Sink builders:
frappe.form.formatters.Color renders:
style="background-color: ${value}"${value} inside <span class="color-value">
frappe.form.formatters.Icon renders:
frappe.utils.icon(value, "md")${value} inside <span class="icon-value">
frappe.utils.icon() also interpolates attacker-controlled icon values into <use ... href="${icon_name}"> without escaping.
DOM insertion: the formatted HTML is inserted into Desk in display mode, making attribute injection possible.
Relevant code:
frappe/frappe/public/js/frappe/form/formatters.js:397-409
frappe/frappe/public/js/frappe/utils/utils.js:1424-1452
frappe/frappe/public/js/frappe/form/controls/base_input.js
frappe/frappe/public/js/frappe/form/controls/color.js
frappe/frappe/public/js/frappe/form/controls/icon.js
frappe/frappe/model/base_document.py
PoC
Color formatter
Log in to Desk as an authenticated user.
Open a document containing a Color field. In the local validation environment, the PoC used the custom DocType XSS Parent and document id.
Intercept the save request with Burp Suite and replace the Color field value with:
red" onmousemove="alert(7441)" x="
Forward the request so the tampered value is stored.
Visit the affected record in Desk:
http://localhost:18080/desk/xss-parent/%3Cdocument_id%3E
Move the mouse over the rendered PoC Color value.
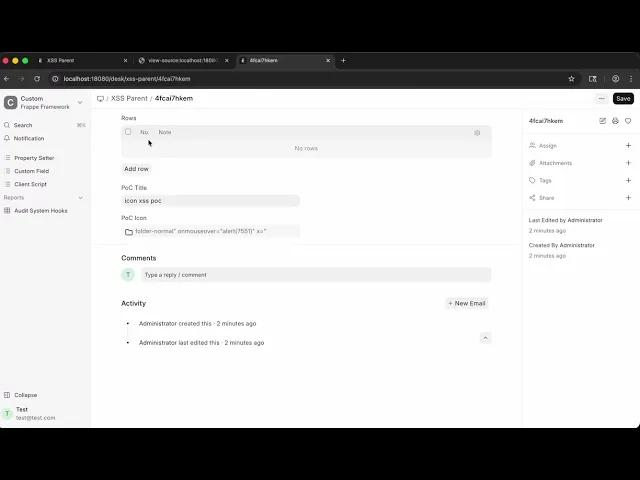
Icon formatter
Log in to Desk as an authenticated user
Open a document containing an Icon field. In the local validation environment, the PoC used the custom DocType XSS Parent and document ID.
Intercept the save request with Burp Suite and replace the Icon field value with:
f
older-normal" onmouseover="alert(7551)" x="
Forward the request so the tampered value is stored.
Visit the affected record in Desk:
http://localhost:18080/desk/xss-parent/document_id
Move the mouse over the rendered PoC Icon value.
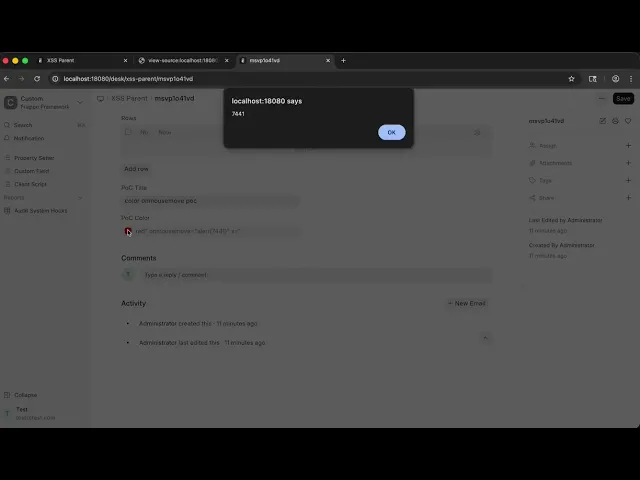
Evidence of Exploitation
Color formatter
Icon formatter
Our security policy
We have reserved the ID CVE-2026-3837 to refer to this issue from now on.
System Information
Frappe
Version: 16.10.0
Operating System: Any
References
Github Repository: https://github.com/frappe/frappe
Mitigation
An updated version of Frappe is available at the vendor page.
Credits
The vulnerability was discovered by Oscar Uribe from Fluid Attacks' Offensive Team using the AI SAST Scanner.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.