
Frappe Framework 16.10.0 - Stored DOM XSS in Tag Pill Renderer
4.6
Medium
Detected by

Fluid Attacks AI SAST Scanner
Disclosed by
Oscar Uribe
Summary
Full name
Frappe Framework 16.10.0 - Stored DOM XSS in Tag Pill Renderer
Code name
State
Public
Release date
Affected product
Frappe
Vendor
Frappe
Affected version(s)
16.10.0
Vulnerability name
Stored cross-site scripting (XSS)
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:H/UI:A/VC:N/VI:N/VA:N/SC:L/SI:L/SA:N
CVSS v4.0 base score
4.6
Exploit available
Yes
CVE ID(s)
Description
An authenticated attacker can store a crafted tag value in _user_tags and trigger JavaScript execution when a victim opens the list/report view where tags are rendered. The vulnerable renderer interpolates tag content into HTML attributes and element content without escaping.
Vulnerability
The vulnerable path is:
1. Source: attacker-controlled tag value via frappe.desk.doctype.tag.tag.add_tag.
2. Persistence: _user_tags stores comma-separated tags.
3. Sink builder: ListView.get_tags_html renders:
title="${tag}"${tag} in inner HTML without escaping.
DOM insertion: rendered row HTML is inserted in list/report view, enabling attribute injection (e.g., onmouseover).
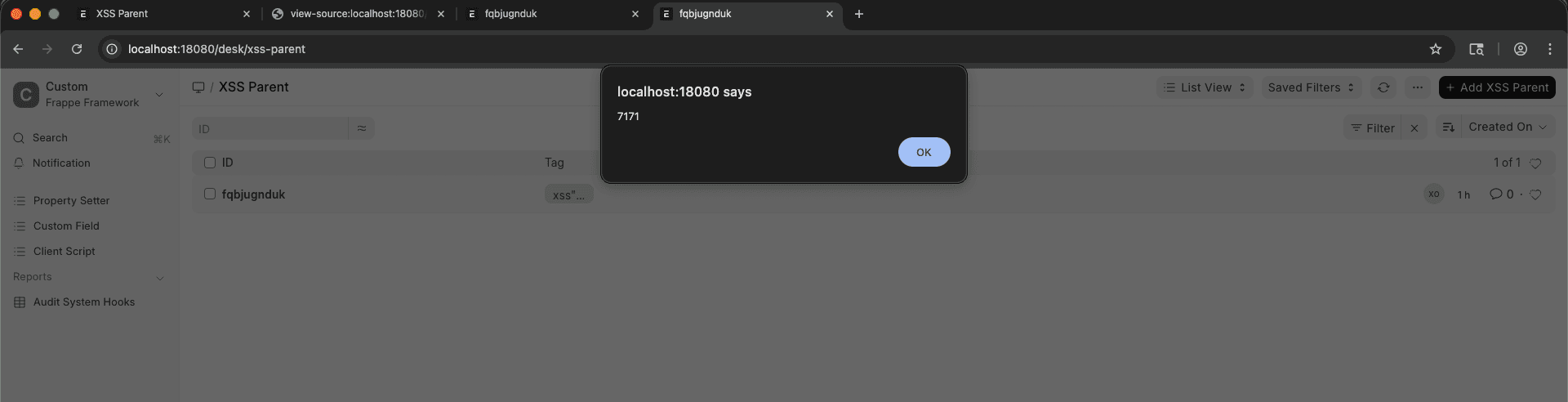
PoC
Visit:
http://localhost:18080/app/xss-parent/view/report
Enable
Show TagsIn list settings, if hiddenMove the cursor over the malicious tag pill
Evidence of Exploitation
Video of exploitation
Static evidence
Our security policy
We have reserved the ID CVE-2026-3673 to refer to this issue from now on.
System Information
Frappe
Version: 16.10.0
Operating System: Any
References
Github Repository: https://github.com/frappe/frappe
Mitigation
There is currently no patch available for this vulnerability.
Credits
The vulnerability was discovered by Oscar Uribe from Fluid Attacks' Offensive Team using the AI SAST Scanner.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.














