Opinions
Beyond detection: what Claude Mythos and Project Glasswing signal for the future of AppSec


Content writer and editor
Updated
9 min
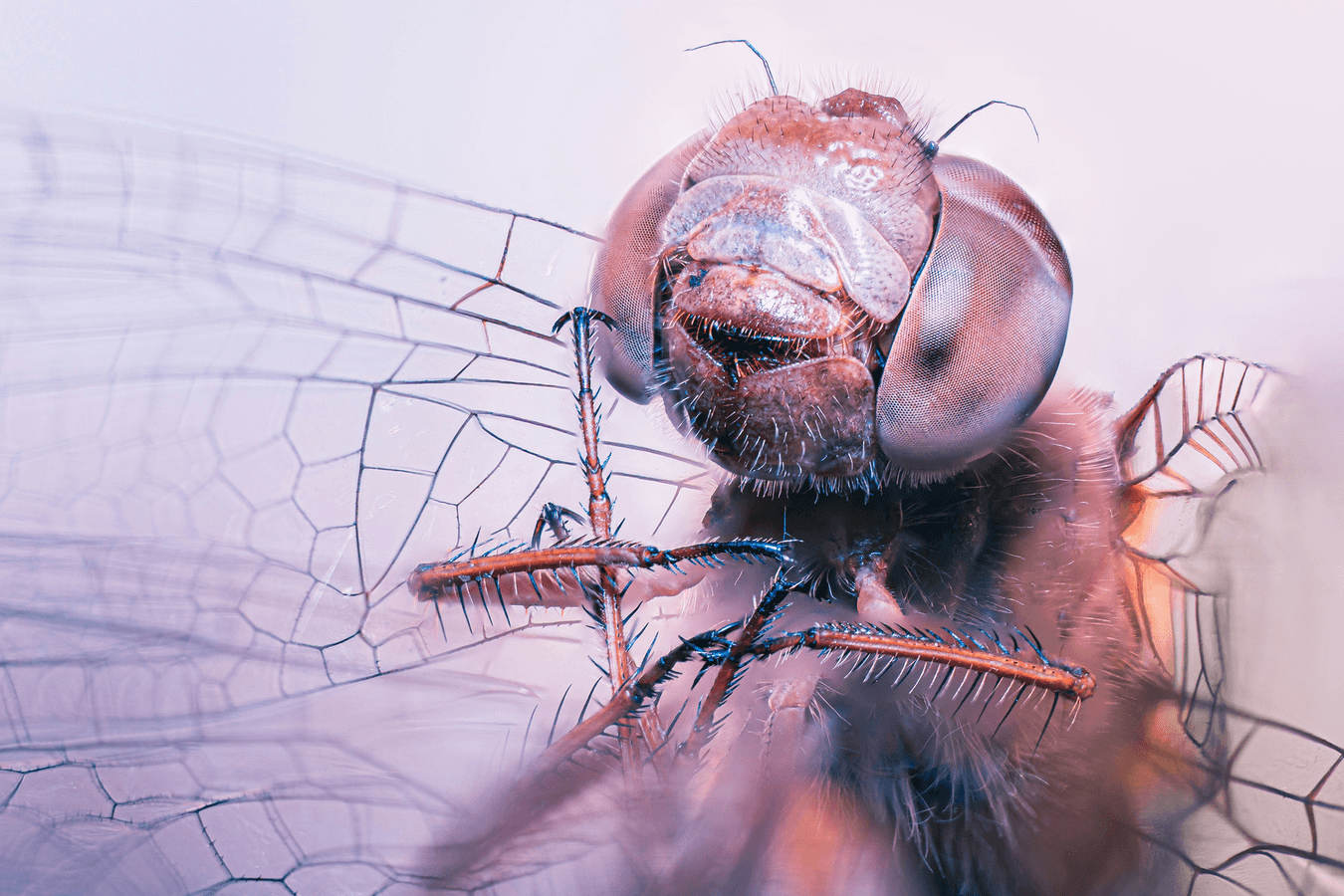
These days, the cybersecurity sector is focusing on a peculiar and seemingly high-stakes narrative: an autonomous AI agent capable of detecting and exploiting vulnerabilities on a scale that previously seemed reserved for state actors. At the center of this conversation are two interconnected initiatives from Anthropic, Claude Mythos Preview and Project Glasswing, and the reactions they have sparked range from alarm to dismissal. Neither of these reactions is particularly useful.
While the marketing machinery surrounding these launches is formidable, the potential implications for application security are fraught with both genuine technical breakthroughs and strategic uncertainty. Rather than asking whether Mythos is revolutionary or overhyped, a more useful question arises: What does this moment reveal about where application security is headed? And, more importantly, what does this require of organizations that need to defend real-world systems today?
What Anthropic put on the table
Claude Mythos Preview is described as a frontier model specifically refined for high-level reasoning and computer security tasks. While previous LLMs focused primarily on static analysis to detect, for example, typical SQL injections in code snippets, Mythos operates as an autonomous ("agentic") system. Its most striking aspect lies not in a single feature but in the combination of capabilities: it reads and reasons about massive codebases, formulates hypotheses about vulnerabilities, dynamically tests those hypotheses, chains multiple weaknesses into viable attack paths, and generates functional exploits alongside reproducible reports.
However, as Rafael Álvarez, Co-founder of Fluid Attacks, notes on his personal blog, this kind of capability does not emerge from a model alone but from a broader system: "a harness around a running system, its source code, deterministic tools that the model orchestrates… and a human who assembles and validates the results."
The Mythos workflow is typically structured as follows: the project in question is loaded into a secure container isolated from the Internet, where multiple instances of the model operate. The model then analyzes the full codebase and ranks files by their security relevance on a scale of 1 to 5 (e.g., a file that processes raw data from the Internet receives a "5," while a configuration file might receive a "1"). Using Claude Code, the model formulates hypotheses about potential flaws, writes debugging logic, executes the code to confirm its suspicions, and iterates.
The prioritization step is also key to scaling the assessments. Instead of scanning entire repositories uniformly, the system ranks files by their likelihood of containing exploitable flaws. It assigns parallel agents to the highest-risk areas first, reducing duplication and increasing efficiency across large codebases.
When it finds something, Mythos autonomously builds a proof-of-concept exploit. Next, a separate instance of the agent acts as a judge, reviewing each finding and filtering out minor or uninteresting issues, retaining only high-severity results, which are validated by human triagers before disclosure. According to reports, internal evaluations indicate that the model has identified vulnerabilities that had persisted for decades, including issues in operating systems and widely deployed libraries that had already been exhaustively scrutinized through other methods.
It is hard to ignore such reports. For instance, Anthropic claims that Mythos detected a 27-year-old vulnerability in the OpenBSD kernel related to TCP SACK options, as well as a 16-year-old bug in FFmpeg that had survived millions of automated tests. According to the company, the model also chained together several Linux kernel vulnerabilities to achieve local privilege escalation on its own. Furthermore, it states that the success rate in generating functional exploits is over 72%, representing a dramatic leap forward compared to previous models (including the recent Opus 4.6), which struggled significantly with zero-day vulnerabilities.
On the other hand, Project Glasswing is the defensive response to the aforementioned capabilities. Recognizing that releasing a tool of this kind without guardrails could have catastrophic consequences, Anthropic assembled a consortium of technology and security companies, including AWS, Google, Microsoft, NVIDIA, Cisco, CrowdStrike, and Palo Alto Networks. The initiative is backed by $100 million in model usage credits and $4 million in donations to open-source security organizations such as Alpha-Omega and OpenSSF.
The stated goal is to provide these partners and open-source maintainers with access to models like Mythos so they can find and fix vulnerabilities in critical software infrastructure before malicious attackers can exploit similar capabilities. At first glance, this resembles previous industry collaborations. However, the underlying premise is different: if vulnerability discovery becomes drastically easier and faster, the entire playbook for defensive strategies should change.
In practice, Glasswing is not just a collaboration agreement but an operational testing environment. Participating organizations are using Mythos Preview to perform tasks such as black-box testing of binaries, endpoint security analysis, and vulnerability discovery across both proprietary and open-source systems, with findings feeding into coordinated disclosure and remediation processes.
Evidence, skepticism, and strategic timing
The debate surrounding Mythos is grounded in a mix of verifiable evidence and uncertainties. On the one hand, claims about AI-driven paradigm shifts have become commonplace, and many practitioners are wary of marketing rhetoric cloaked in technical ambition. On the other hand, there is tangible evidence of real vulnerabilities discovered and remediated in widely used systems, and reputable organizations have rallied around a shared concern.
These are concrete contributions, not hypothetical demonstrations. Still, the public evidence remains much smaller than the claim set (apparently, responsible disclosure timelines prevent a full inspection). Anthropic claims that less than 1% of the potential vulnerabilities discovered so far have been fully patched, and that it has identified "thousands" of high- and critical-severity vulnerabilities. However, at this stage, the public record consists mainly of a limited set of SHA-3 hash commitments—numbering just over 15 so far—and only one CVE explicitly attributable to Project Glasswing: CVE-2026-4747, listed in the NVD as a FreeBSD RPCSEC_GSS stack-based buffer overflow.
Key operational details remain unclear as well. Álvarez points out that metrics such as false-positive rates, cost in tokens, and validation workflows have not been disclosed, making it difficult to assess the process's true efficiency and reliability in practice.
This ambiguity fuels a familiar cycle of hype and counter-hype, in which both exaggerated optimism and fear coexist. It is worth maintaining a healthy dose of skepticism and asking why Anthropic chose this specific moment to frame its model as too dangerous for public release. The company, for example, is in a fierce race with OpenAI for market dominance and is reportedly heading toward an initial public offering (IPO). A model positioned as too powerful to be released is a compelling narrative for investors and for securing funding in the years to come. Some critics have labeled this "criti-hype," a dynamic in which warnings about a technology's dangers inflate its perceived value. If a tool is powerful enough to destabilize the internet, according to this argument, it must also be powerful enough to justify a multibillion-dollar valuation. Other observers see all of this as early signs of a genuine inflection point.
A balanced reading acknowledges both elements. It is undeniable that there is a marketing strategy behind it, but there is also enough technical substance to warrant serious attention. The historical parallel is instructive: at the time, GPT-2 was considered too dangerous to release to the market, but it was ultimately made available to the public without the predicted catastrophe occurring. Some analysts suspect that Mythos is simply in a beta phase and that the security discourse serves as a convenient cover for working out rough edges with trusted partners before a broader launch. In any case, all of this creates a natural tension: the industry is being asked to prepare to deal with capabilities that cannot yet be fully assessed.
That tension became even sharper shortly after the Mythos and Glasswing announcements. Some researchers reported what they described as a systemic flaw in Anthropic’s Model Context Protocol (MCP), involving STDIO-based configurations that could lead to arbitrary command execution across affected implementations. According to them, the issue affected a large part of the AI supply chain, and Anthropic confirmed the behavior is by design, leaving sanitization to developers rather than changing the protocol. This followed another incident in which Claude Code was shipped to npm with an unintended source map that exposed more than 500,000 lines of proprietary source code, which Anthropic attributed to human error rather than a security breach. Neither episode disproves Mythos’s capabilities, but both reinforce an uncomfortable point: even the builders of frontier security tools remain subject to the same messy realities of software design, supply chains, release processes, and human oversight as everyone else.
Gated access and the question of equity
The decision to limit Mythos to a closed group of vetted partners raises a separate set of concerns. By concentrating the most powerful defensive tools behind a consortium of tech giants, Anthropic risks creating a two-tier security landscape. Large enterprises with the resources to participate in Glasswing will have early access to these capabilities. Small and medium-sized businesses, unable to absorb the future pricing or the infrastructure requirements to run these agents, could find themselves permanently disadvantaged, still facing AI-augmented attackers but without AI-grade defenses.
There are also open questions about governance and dependency. Organizations that rely on Mythos-class tools through Glasswing become dependent on Anthropic's decisions about access, pricing, and continued availability. Centralization of this kind deserves scrutiny, especially when the stakes involve critical infrastructure.
The real shift: discovery becomes a common good
The most consequential implication of Mythos and Glasswing is not the discovery of new flaws. It is the devaluation of the discovery itself. We are approaching a reality in which the detection of vulnerabilities is abundant and cheap, meaning that it is no longer the key differentiator of an AppSec solution; however, the ability to fix those issues remains partially human, finite, and—in the case of open source—largely voluntary. The bottleneck shifts from the security researcher to the software maintainer. This shift also exposes a more immediate issue: most organizations are already aware of many of their vulnerabilities and are simply not remediating them. As Álvarez observes, the problem is often not discovery but discipline—teams "know exactly what is broken, and they are not fixing it."
This is not theoretical. Many organizations are already accumulating more findings than they can reasonably address. Tools like Mythos would take that trend to the extreme. Tools got faster, coverage improved, and the pile of unresolved findings kept growing. Perhaps what's missing now isn't more detection. It's the ability to understand and decide which issues are most important, prioritize them based on context, fix them safely, and verify that the risk actually went down. That also requires a normalized and centralized view of findings across sources; otherwise, AI-generated reports become one more silo added to scanner outputs, pentest reports, tickets and spreadsheets.
Anthropic also notes that traditional benchmarks are no longer sufficient to evaluate these systems, as models can memorize known vulnerabilities. Instead, they focus on zero-day discovery as a more reliable indicator of genuine capability, since such findings cannot originate from training data.
The maintainer burden and the CVE backlog
For open-source developers, the influx of AI-generated vulnerability reports is a double-edged sword. Maintainers of some projects have acknowledged that AI reports are improving in quality, moving from noise to something genuinely useful. But even a high-quality report requires human time to validate, merge, and test. The capacity to absorb that volume of findings and remediate them does not scale the same way discovery does.
Furthermore, the existing CVE ecosystem is already under strain. An exponential increase in vulnerability discovery could overwhelm triage infrastructure, producing backlogs that stretch for months. This creates a dangerous "compliance gap": traditional patching schedules become obsolete when an adversary can move from discovery to exploit in minutes.
AI on both sides
AI-driven vulnerability discovery is not a future scenario. Adversaries are already using AI to scale their operations. Models do not need to reach Mythos-level capabilities to be effective; even moderately capable systems accelerate reconnaissance, exploit development, and attack automation. We have already seen automated data extortion schemes and "vibe hacking" campaigns that once required entire criminal teams. Defenders are compelled to respond with similar tools, but speed alone is not enough. Organizations must also improve the quality of decision-making under time pressure.
It should be noted that one of Mythos's more technically significant capabilities is chaining multiple vulnerabilities to bypass defense-in-depth mechanisms such as KASLR (kernel address space layout randomization) or sandbox isolation. This reflects a shift in which mitigations that rely on increasing the attacker's effort, rather than enforcing hard constraints, may become less effective against AI-assisted workflows.
Critical uncertainties
Despite the momentum, several limitations deserve acknowledgment. First, no system, AI or otherwise, can realistically guarantee complete vulnerability coverage. Different techniques uncover different classes of issues, and false negatives remain a fundamental concern. There is also a more fundamental limitation. As Álvarez explains, software security is not a fully solvable problem in the general case: determining whether a program is free of vulnerabilities is subject to the same theoretical limits described by Rice’s theorem. In practice, this means that any tool—AI-based or not—will always operate through approximation, balancing false positives and false negatives.
Second, the assumption that discovery will become trivial may be overstated. While AI can significantly improve efficiency, large-scale, high-confidence validation still requires resources, context, and human judgment. And the broader ecosystem, particularly open-source maintainers, may simply not have the capacity to absorb the increased volume of findings.
Moreover, data centers have relatively mature patching processes, but the world of operational technology, IoT, and cyber-physical systems does not. There is no equivalent of Windows Update for a water treatment plant's pump controller. If vulnerability discovery becomes OS-agnostic but remediation remains hardware- and environment-specific, we face a wave of zero-days in systems that were never designed to be patched at scale.
What this means for security programs
Taken together, these trends point to a structural shift, not a single technological breakthrough. Several potential consequences follow:
Penetration testing by experts and vulnerability scanning using deterministic tools will continue to lose significant value if they are not used in conjunction with advanced AI models and are not part of comprehensive security programs.
New service models—such as the one already established and offered by Fluid Attacks years ago—will emerge around solutions that integrate discovery, prioritization, remediation, and verification into a continuous workflow.
Security roles will evolve, and the most in-demand skills will shift from detecting vulnerabilities in systems to orchestrating AI agents, accurately validating their results, and making high-impact decisions on risk prioritization and mitigation.
The key question organizations ask when evaluating security providers will no longer focus so much on vulnerability detection capabilities, but rather on the skills to accurately validate findings, prioritize them based on context, and promote rapid, continuous remediation at scale.
As AI-driven security becomes more prevalent, regulatory requirements for auditability, oversight, and accountability will expand. The EU AI Act and NIST frameworks already point in this direction, and "reasonable care" will increasingly require documented human oversight of automated findings.
An autonomous AI discovering a bug and pushing a patch straight to production is a recipe for system failure. The safer model is a closed loop: assign ownership, track remediation, re-test the fix, and keep evidence that the vulnerability is no longer exploitable. Continuous verification, red-teaming of AI-generated fixes, and integration between scanners, management platforms, and the developers who implement changes are all essential safeguards.
These changes are already underway. Claude Mythos Preview simply accelerates them.
Beyond detection: where the value lies
For companies like Fluid Attacks, this moment reinforces a strategic direction rather than introducing a new one. Application security has never been only about finding vulnerabilities. Effective programs require continuous visibility into code and infrastructure, context-aware prioritization, practical remediation guidance, and verification that fixes actually reduce risk exposure.
AI agents can enhance each of these areas, but they cannot replace the need for an integrated approach. Beyond what AI currently offers in terms of detection capabilities—above all—and remediation, human expertise provides the interpretation and prioritization that allow a CISO to make high-stakes decisions under pressure. Security engineers may no longer be the primary finders; they are mainly deciders.
Even in this agentic era, the core mission of a robust AppSec solution like Fluid Attacks remains unchanged. The most valuable platforms going forward will be those that translate findings into actionable decisions, coordinate remediation at scale, provide evidence of risk reduction, and integrate into real development and production environments. Communicating that value requires a shift too: instead of emphasizing the volume of vulnerabilities found, organizations need to demonstrate their ability to reduce risk effectively and consistently.
Conclusions
If anything, increased development speed driven by AI may expand the total attack surface. More code, even at lower vulnerability density, can still result in more vulnerabilities overall. Organizations should not be lulled into a false sense of security by the promise of an "AI savior." The race between automated attackers and automated defenders is in full swing. It may be only 18 months before capabilities like Mythos's become widely available. The question leadership must ask is not whether to adopt a more advanced model, but whether the organization has the architecture, identity governance, and human expertise necessary to operate in a world where both attackers and defenders use it.
Claude Mythos and Project Glasswing do not spell the end of cybersecurity as we know it. They mark an acceleration of trends that were already underway. Detection is becoming faster and more automated. Remediation lags slightly behind because it remains more complex, resource-intensive, and context-dependent (this does not mean that AI-driven remediation won't advance soon). For now, the gap between detection and action becomes the defining challenge. For the cybersecurity industry, the implication is straightforward: the future belongs to those who can bridge that gap.
A truly robust AppSec solution must go beyond the fairly compelling discovery of zero-day vulnerabilities to offer an operational model based on comprehensiveness, scalability, sequencing, and change control. Fluid Attacks achieves this by leveraging artificial intelligence, risk detection and management tools, and human judgment and creativity to ensure your software's security. We invite you to contact us to start enjoying our AppSec solution.
Get started with Fluid Attacks' ASPM solution right now
Other posts