Opinions
Fluid Attacks at the OAS Cyber Americas Cup 2026


Security analyst
5 min
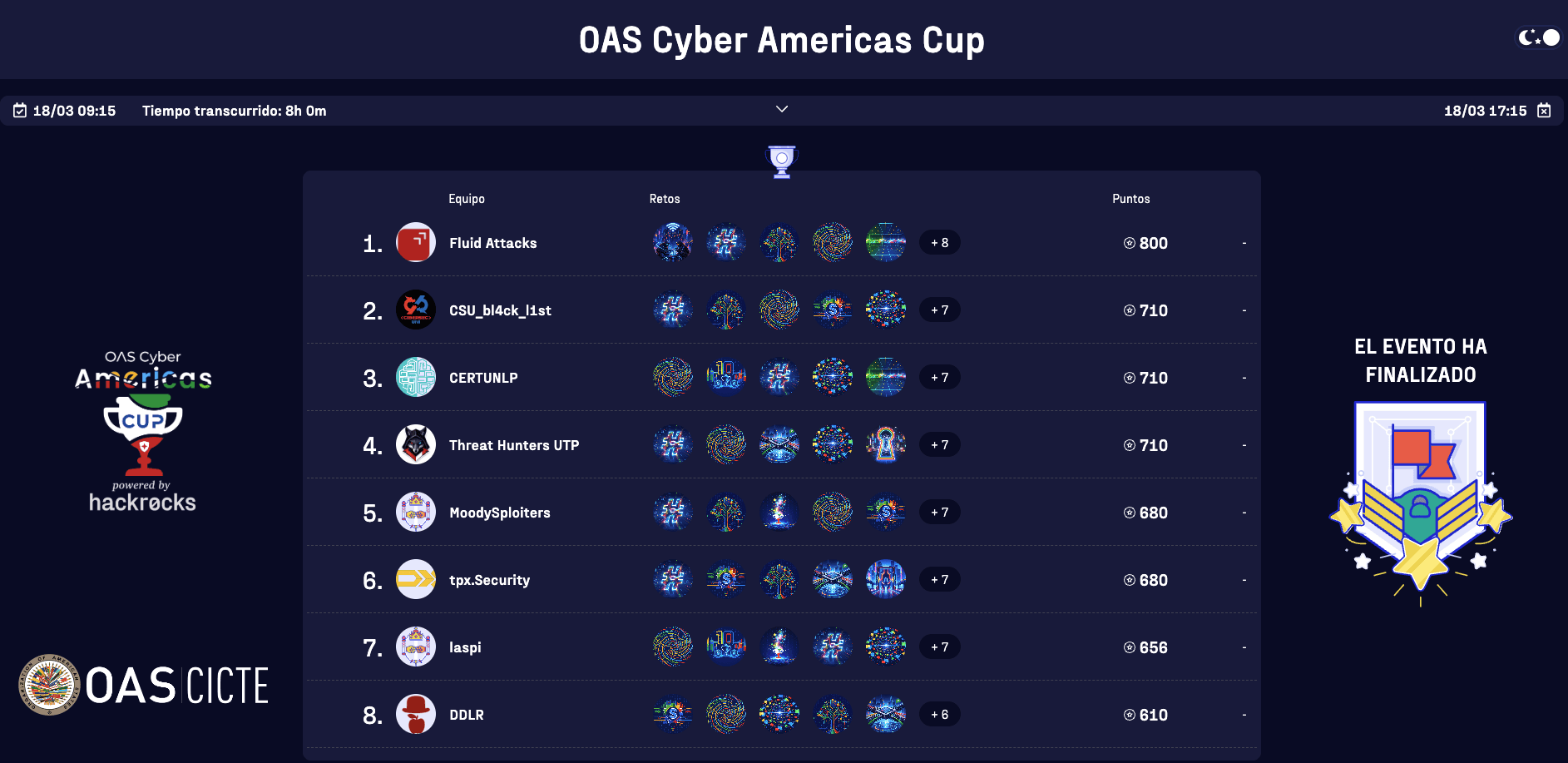
The Fluid Attacks CTF team recently had the opportunity to compete in the OAS Cyber Americas Cup. In this post, we'll dive into our experience participating in the inaugural edition of this CTF, competing against 831 hackers spread across 224 teams, and how we managed to take home first place after an intense 8-hour contest.
This competition was organized by the Cybersecurity Section of the Inter-American Committee against Terrorism (CICTE) of the Organization of American States (OAS), with support from Hackrocks—a cybersecurity training platform focused on hands-on learning through CTFs. The event aimed to promote real-world incident response capabilities and foster regional cooperation.
The road to the competition
We first heard about the event through an OAS post on LinkedIn and immediately knew we had to assemble a team. The rules required teams of 3 to 4 members, and all participants had to use a non-generic email address (i.e., from a company, university, or government entity).

The CTF categories included Cryptography, Forensics, Web Hacking, Reversing, and Network Security. As part of our standard preparation, we meticulously reviewed the CTF rules to ensure we had total clarity on what was permitted, avoiding any infractions and competing fairly from the jump. With the strategy set, we formed our team and completed the registration.
The competition was scheduled for March 18, 2026, but all teams had to pass an approval process first. We received the green light on March 16—we were officially ready to go.
As part of the methodology we are refining for the HTB Business CTF, we decided to meet in person at a hotel in Medellín throughout the competition. We had a comfortable room, screens, a whiteboard for brainstorming, multiple connection points, a stable network, meals included, and, above all, the internet and bandwidth to support the CTF's dynamics adequately. This allowed us to focus entirely on the game, without distractions or logistical or technical limitations.
This was all made possible by Simón Correa, our Head of Research, who leads the CTF initiative, as well as the marketing team, management, and other colleagues at Fluid Attacks. In the weeks leading up to the event, he evaluated various hotels and coworking spaces to find the best fit for our technical needs, prioritizing the in-person collaboration we found so effective during last year's HTB Business.
With everything in place, Cristian Vargas, Adrián Castañeda, Camilo Vera (who Fluid Attacks flew in from Chile), and I were ready for the challenge.
The calm before the exploits
The CTF kicked off at 9:15 a.m. (UTC-5), but we gathered at 7:30 a.m. to test connections, access the platform, and set up our environments. We made sure to grab breakfast together first to break the ice and get in the right headspace.
At 9:00 a.m., we joined a Zoom meeting where the organizers welcomed the teams and shared some impressive stats:
835 hackers were registered across 225 teams from various OAS member countries.
136 female hackers were participating—in my experience, one of the highest levels of female representation I've seen in this type of event.
Then came the announcement everyone was waiting for—the prizes:
1st place: 4 tickets, including flights and accommodation, to the OAS Cybersecurity Symposium this October.
2nd place: 4 passes to the 2026 Cybersecurity Summer Bootcamp in Spain (hotel and event invitations included). We do not yet have flight information.
3rd place: 2 passes to the 2026 Cybersecurity Summer Bootcamp in Spain (hotel and event invitations included). We have the same question as in the second place.
At that point, the motivation was through the roof.
Game on
Once the meeting ended, the CTF began and was scheduled to last 8 hours; in other words, it would run until 5:15 p.m. (UTC-5). We initially split into categories where we felt we could contribute the most, given our individual expertise, and just a couple of minutes later, the first flags started coming in for the less difficult challenges.
The organizers initially released 12 challenges. Thanks to a mix of teamwork and individual skill, we cleared these first exercises in under two hours. The final challenge of the initial batch—a hybrid of Web Hacking and Cryptography—gave us a bit of trouble, but after some trial and error, we secured the flag.

We submitted that final flag just three minutes before the second-place team. It was a tight race, and we were thrilled to hold the lead.
Throughout the CTF, we leveraged AI to assist us, proving how this technology can be a force multiplier. When combined with human expertise, AI can maximize performance by automating tedious tasks or helping to script solutions once the core problem is identified.
However, it wasn't all smooth sailing. We experienced significant platform lag. While some challenges still worked, we couldn't see the scoreboard or submit the flags we had already captured. The organizers later mentioned the platform suffered what appeared to be a DDoS attack—something you definitely don't expect at a hacking competition!
Since we had finished the available challenges (after a couple of hours, they confirmed they would indeed add two more), we used the downtime to document our write-ups and discuss our solutions. We also took a break for lunch and to talk about the CTF; even in a high-level competition, we're human and need time to recharge.
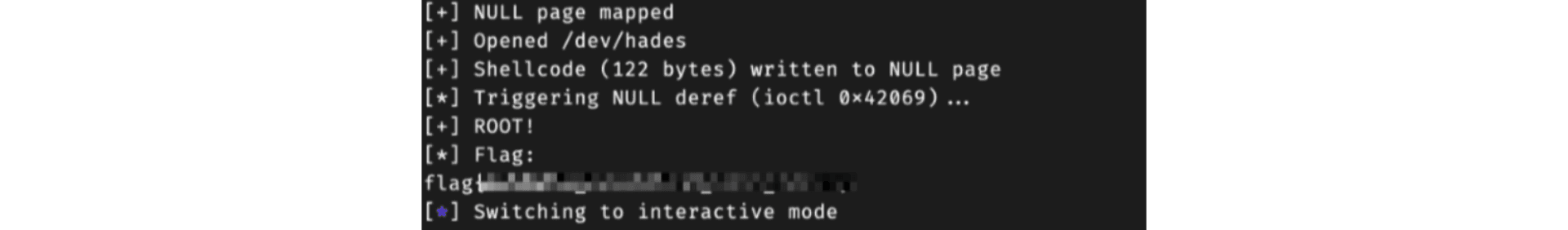
With about three hours left on the clock, two additional binary exploitation challenges were released: one focused on heap and the other on kernel exploitation. We dropped the documentation and got back to work. We solved the heap challenge despite not having a local test environment, which made it tricky, but we eventually found the flag. The final kernel challenge was frustrating because while the team had a working exploit locally, the remote environment wasn't responding correctly.
Curiously, just as we got back to writing our write-ups, we noticed the environment for the missing challenge was functional again. So, after the event, we ran our exploits and captured the flag. Unfortunately for me, though fortunately for our team, Camilo completed the challenge three seconds earlier, and we both sent the flag to our private group at almost the same time, which led to a few laughs.
GG, well played
After 8 hours of intense competition, brainstorming, and occasional frustration, we secured 1st place out of 185 teams that solved at least one challenge. We successfully cleared 13 out of 14 challenges during the event and finished the final one shortly after.
Looking back, the most important part of these events—regardless of the result—is having fun, connecting with people who share your passion, and learning something new. That curiosity is what keeps us coming back. After a CTF like this, you always walk away as a better hacker with sharper communication and teamwork skills.
In the end, we couldn't let the day go by without getting together to celebrate and spend time with our colleagues, especially since Camilo was visiting from Chile. These experiences wouldn't be possible without the support of Fluid Attacks, which allows us to test our skills in these arenas so we can continue to grow and offer our clients the very best.
On a final note, we want to offer some constructive feedback. The initiative behind the OAS Cyber Americas Cup is incredibly valuable for the region. However, there is room for improvement in organization. Platform stability, support response times, and overall coordination were not quite up to the level a competition of this scale deserves. We say this with respect and honesty: when you bring together hundreds of hackers from across the region, the participant experience must be a top priority. We hope future editions match the high ambition of the event's mission.
Thanks for reading. Hack the planet!
Get started with Fluid Attacks' PTaaS right now
Other posts