Risk-based vulnerability management (RBVM)
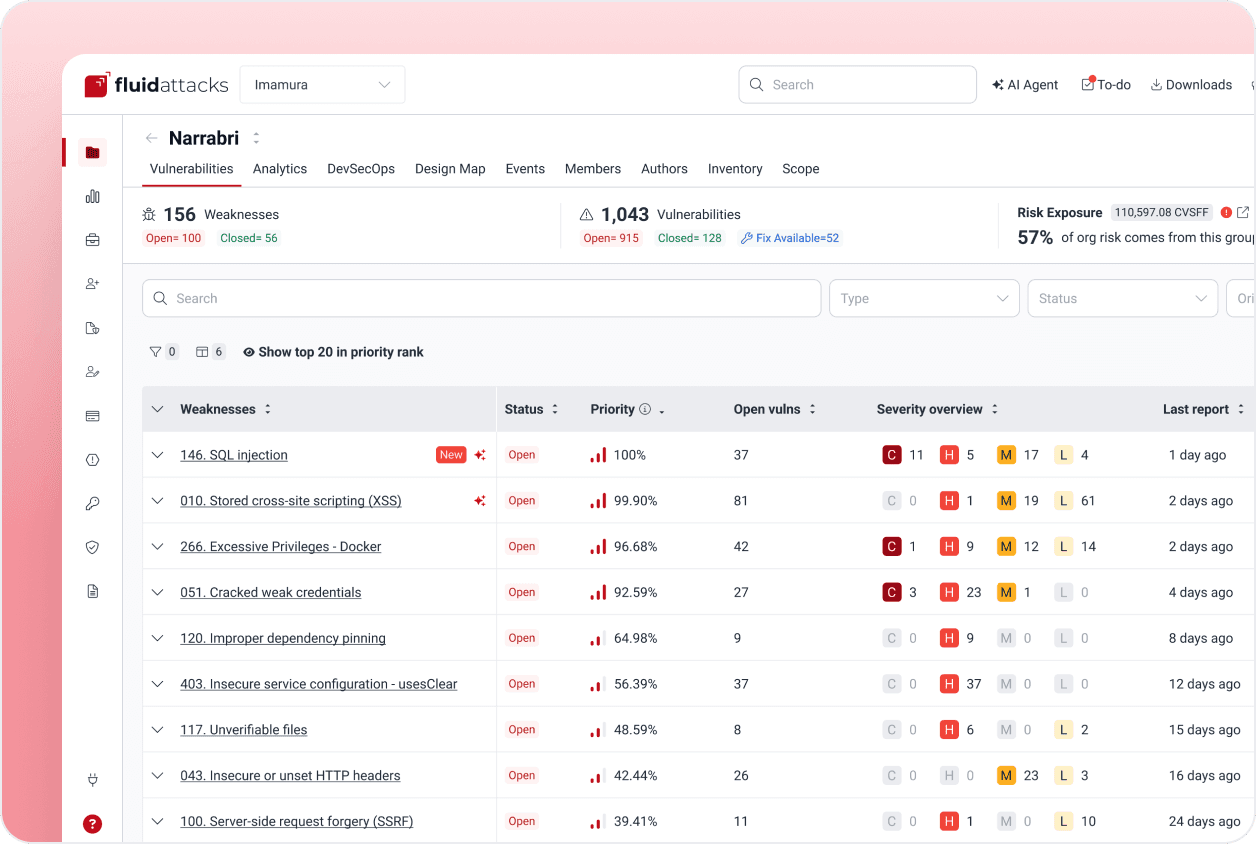
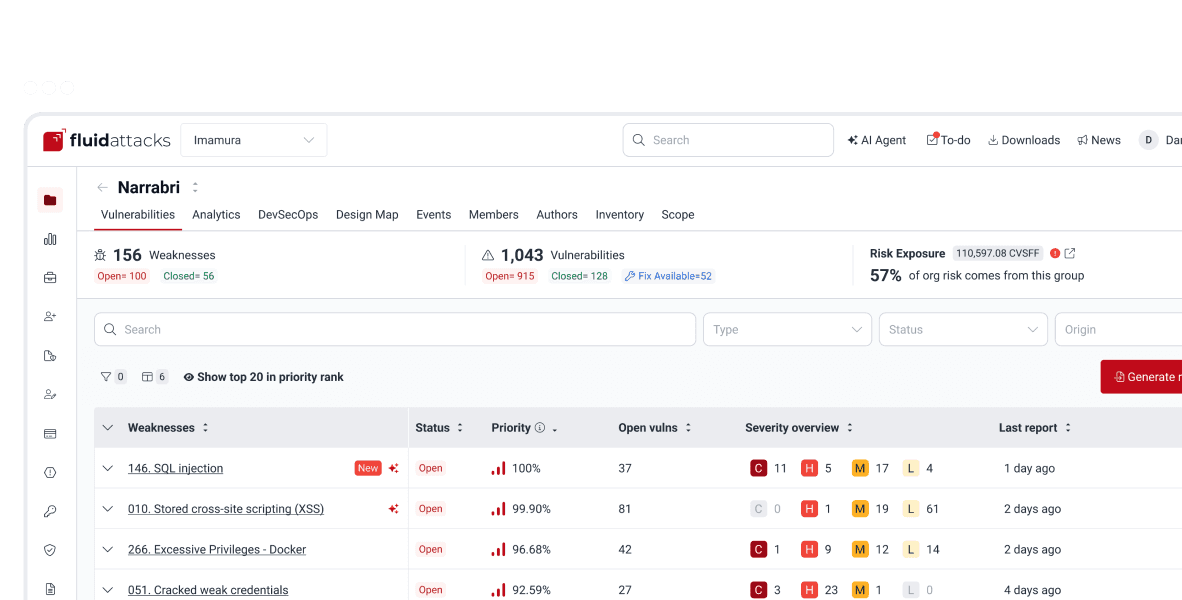
Prioritize and remediate your systems' security issues
Vulnerability reports focused on your organization's risk exposure
One dashboard to understand security flaws and assign their remediation
Support by our pentesters and vulnerability remediation assisted by GenAI

Companies already benefiting from Fluid Attacks' risk-based vulnerability management solution
Frequently asked questions
What is vulnerability management?
What is a vulnerability management program?
What is risk-based vulnerability management?
How is risk-based vulnerability management different from legacy vulnerability management?
What is Fluid Attacks' CVSSF metric?
Do you want to learn more about risk-based vulnerability management?
Read some of our posts related to this solution.
RBVM is a crucial piece of Fluid Attacks' solution
We offer an all-in-one solution that combines our AI, automated tools and pentesters to help you improve your cybersecurity posture continuously.