
Askbot 0.12.2 - Insecure Direct Object Reference (IDOR)
5,3
Medium
Discovered by
External researcher
Summary
Full name
Askbot 0.12.2 - Insecure Direct Object Reference (IDOR) in upload an avatar
Code name
State
Public
Release date
Affected product
Askbot
Vendor
Askbot
Affected version(s)
0.12.2
Package manager
pypi
Vulnerability name
Insecure object reference
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N
CVSS v4.0 base score
5.3
Exploit available
No
CVE ID(s)
Description
All versions of askbot before and including 0.12.2 allow an attacker authenticated with normal user permissions to modify the profile picture of other application users. This is possible because the application does not properly validate user authorization when handling profile avatar updates. By intercepting and modifying the POST request used to change the profile picture, an attacker can alter the user_id parameter and update the avatar of any user in the application. The issue occurs in the avatar_view.py file, specifically in the admin_or_owner_require.
Vulnerability
This vulnerability occurs because the application is vulnerable to Insecure Direct Object Reference (IDOR). The admin_or_owner_required function incorrectly validates user permissions by comparing the authenticated user ID with a user_id value supplied by the client, which can be manipulated. As a result, the application fails to enforce proper access control, allowing unauthorized users to perform actions on resources belonging to other users.
PoC
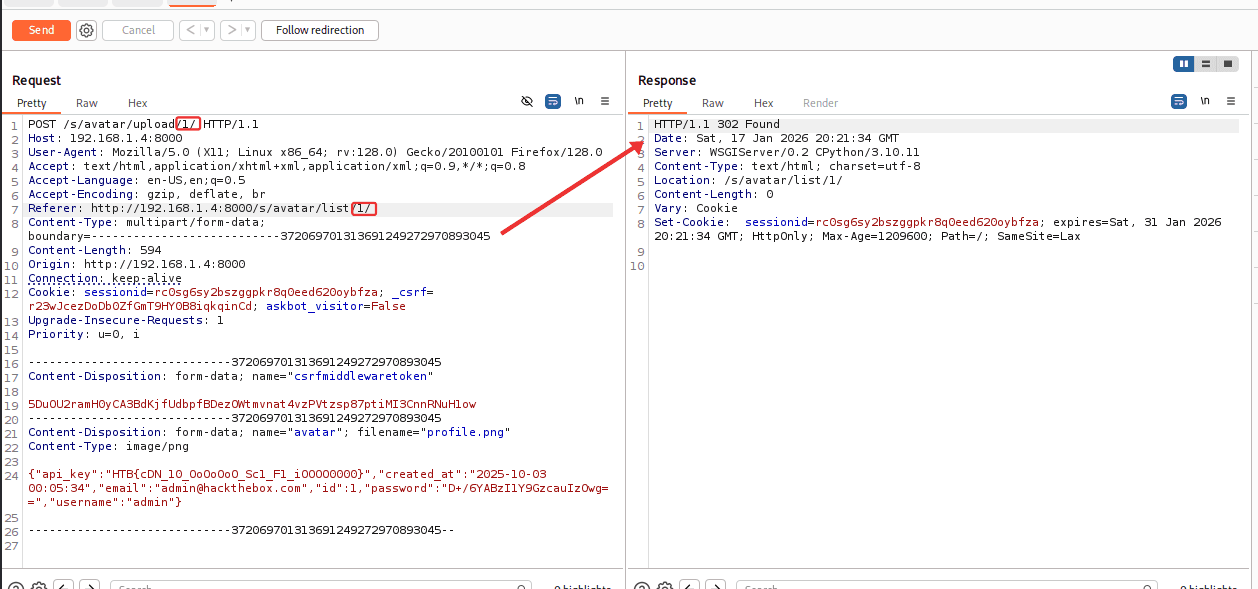
Evidence of Exploitation
Our security policy
We have reserved the ID CVE-2026-1213 to refer to this issue from now on.
System Information
Askbot
Version 0.12.2
Operating System: Any
References
Github Repository: https://github.com/ASKBOT/askbot-devel
Patch: https://github.com/ASKBOT/askbot-devel/commit/3da3d75f35204aa71633c7a315327ba39cb6295d
Mitigation
An updated version of Askbot is available at the vendor page.
Credits
The vulnerability was discovered by Daniel Celis, an independent security researcher.
Timeline
Vulnerability discovered
Vendor contacted
Vendor replied
Follow-up with vendor
Vendor confirmed
Vulnerability patched
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.








