OpenSupports 4.11.0 — SQL Injection
7,1
High
Discovered by

Offensive Team, Fluid Attacks
Summary
Full name
OpenSupports 4.11.0 — SQL Injection in staff “get-new-tickets” endpoint
Code name
State
Public
Release date
Affected product
OpenSupports
Vendor
OpenSupports
Affected version(s)
4.11.0
Vulnerability name
SQL Injection
Vulnerability type
Remotely exploitable
Yes
CVSS v4.0 vector string
CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:L/VA:N/SC:N/SI:N/SA:N
CVSS v4.0 base score
7.1
Exploit available
Yes
CVE ID(s)
Description
The endpoint POST /api/staff/get-new-tickets concatenates the user-controlled parameter departmentId directly into the SQL WHERE clause without parameter binding. As a result, an authenticated staff user (level ≥ 1) can inject SQL to alter the filter logic (e.g., tautologies or time-based primitives), effectively bypassing department scoping and disclosing tickets beyond their intended access.
Vulnerability
Relevant backend fragments:
Vulnerable concatenation (server/controllers/staff/get-new-tickets.php):
Secure pattern for comparison (server/controllers/staff/get-tickets.php):
Confidentiality breach: a low-privileged staff user can list “new tickets” across all departments by injecting into the department filter, gaining visibility into titles, content excerpts, and metadata.
Scope escalation: bypass of authorization-by-filter (department-based access control) in the “new tickets” view.
PoC
Log in as a staff user (level 1) and extract CSRF:
Baseline request (no injection):
Tautology injection — expand scope to all departments:
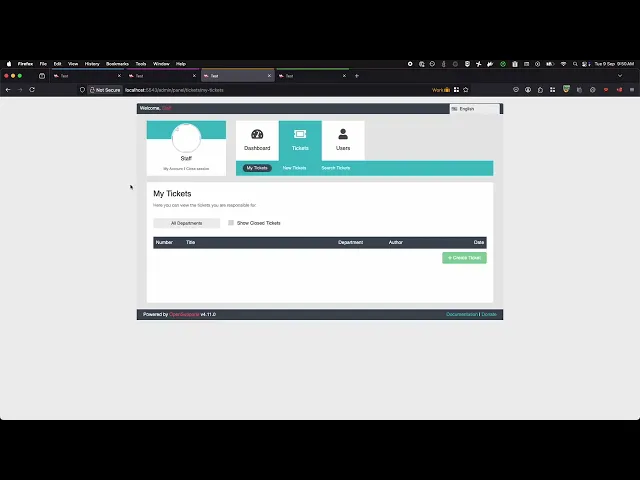
Evidence of Exploitation
Our security policy
We have reserved the ID CVE-2025-10692 to refer to this issue from now on.
System Information
OpenSupports
Version 4.11.0
Operating System: Any
References
Github Repository: https://github.com/opensupports/opensupports
Security: https://github.com/opensupports/opensupports/security
Mitigation
There is currently no patch available for this vulnerability.
Credits
The vulnerability was discovered by Cristian Vargas from Fluid Attacks' Offensive Team.
Timeline
Vulnerability discovered
Vendor contacted
Public disclosure
Does your application use this vulnerable software?
During our free trial, our tools assess your application, identify vulnerabilities, and provide recommendations for their remediation.








